
Search
From AI model to human ear, Telnyx powers every step with low-latency voice.
From telnyx.com
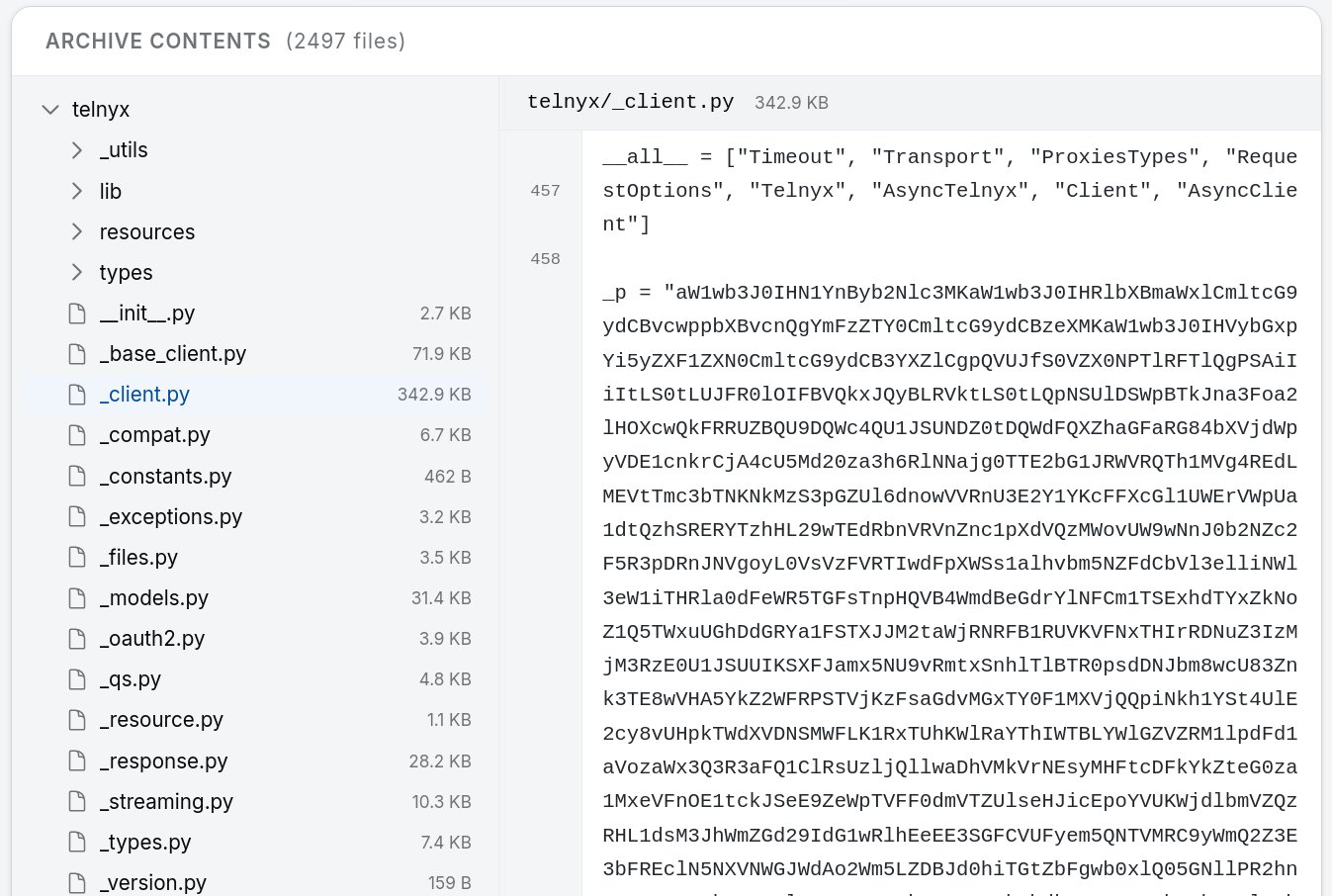
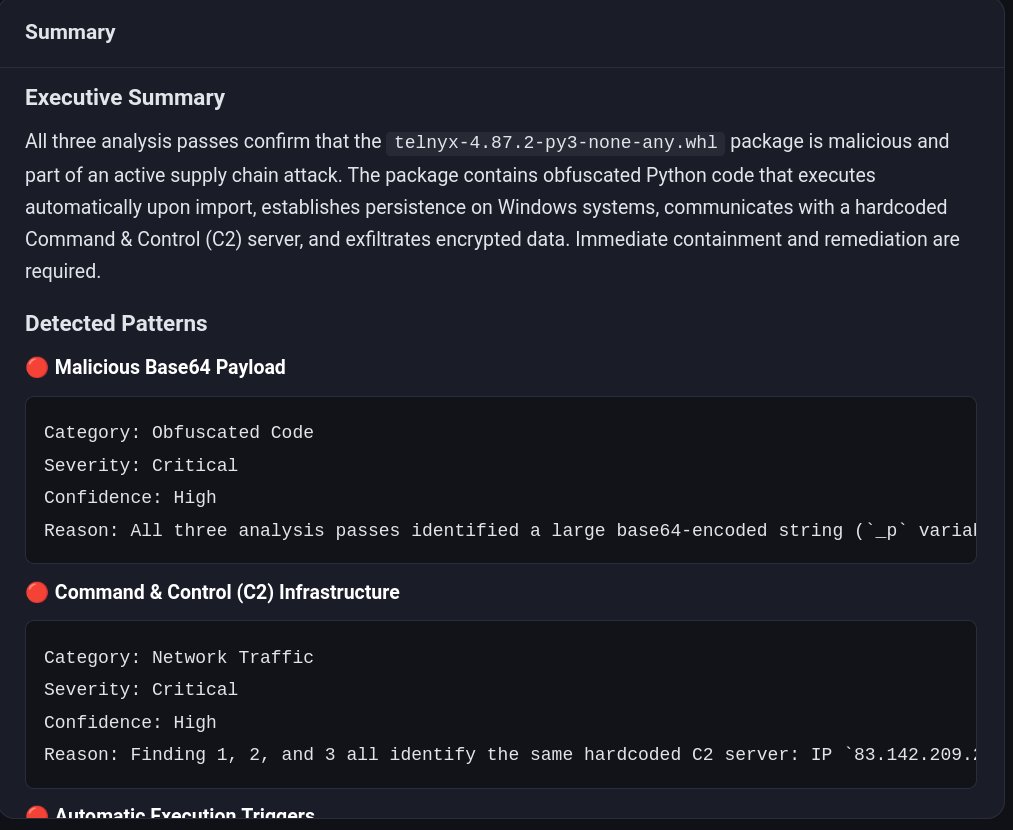
Malicious telnyx 4.87.1/4.87.2 on PyPI used audio steganography March 27, 2026, enabling cross-platform credential theft.
From thehackernews.com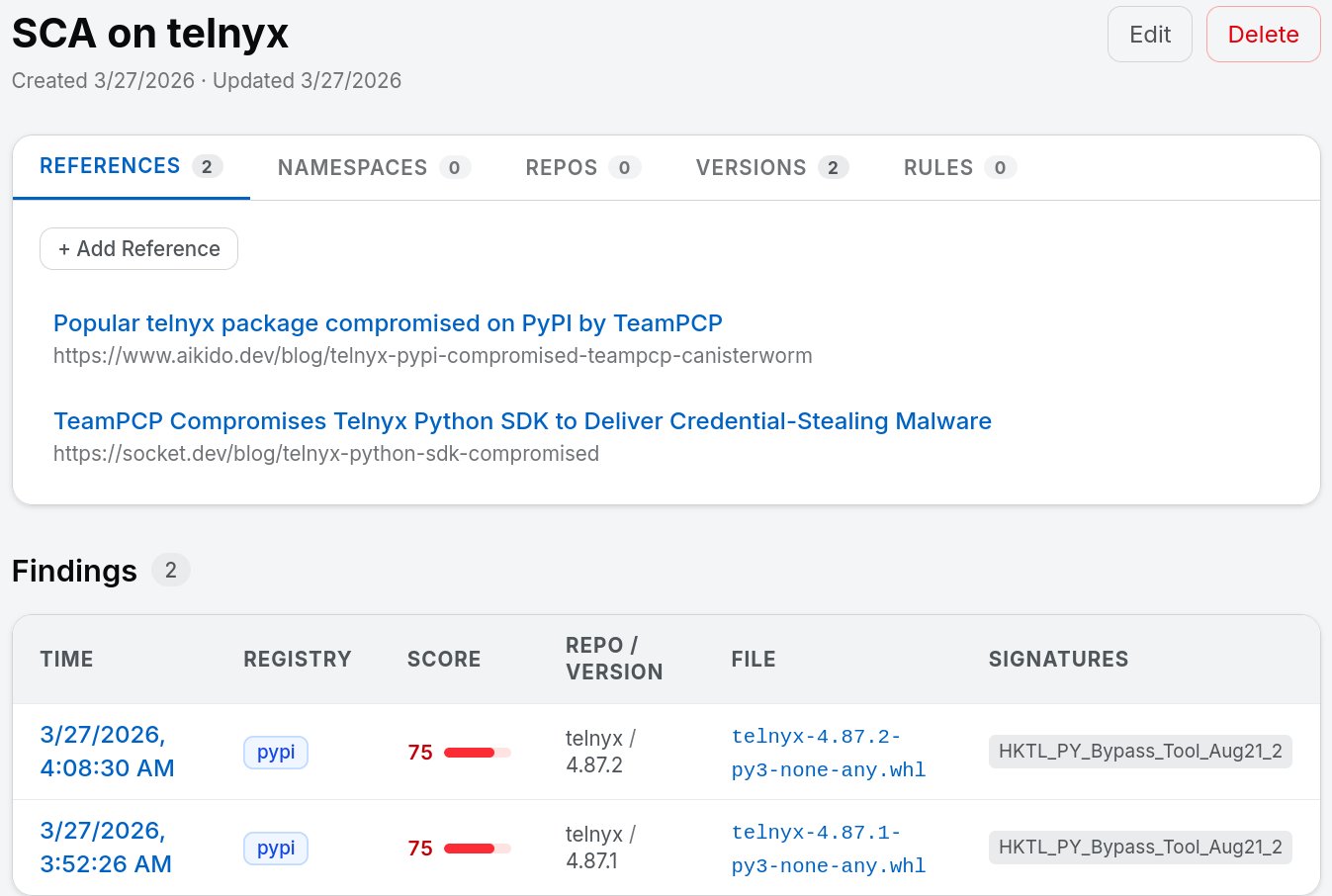
On March 24, 2026, versions 1.82.7 and 1.82.8 of LiteLLM — with ~97 million monthly downloads — were found to contain a credential-stealing backdoor. Here's what happened, how it worked, and what you...
From techlife.blog

Explore the security breach of LiteLLM, affecting millions of users with multi-stage payloads and devastating consequences.
From xygeni.ioExplore the security breach of LiteLLM, affecting millions of users with multi-stage payloads and devastating consequences.
From xygeni.io
A new supply chain attack has compromised LiteLLM on PyPI with credential-stealing malware in a library with 95 million monthly downloads.
From cyberinsider.comCompromised litellm PyPI versions delivered a multi-stage credential stealer, exposing AI pipelines and cloud secrets in a targeted supply chain attack.
From sonatype.com
The TeamPCP hacking group continues its supply-chain rampage, now compromising the massively popular "LiteLLM" Python package on PyPI and claiming to have stolen data from hundreds of thousands of...
From bleepingcomputer.com