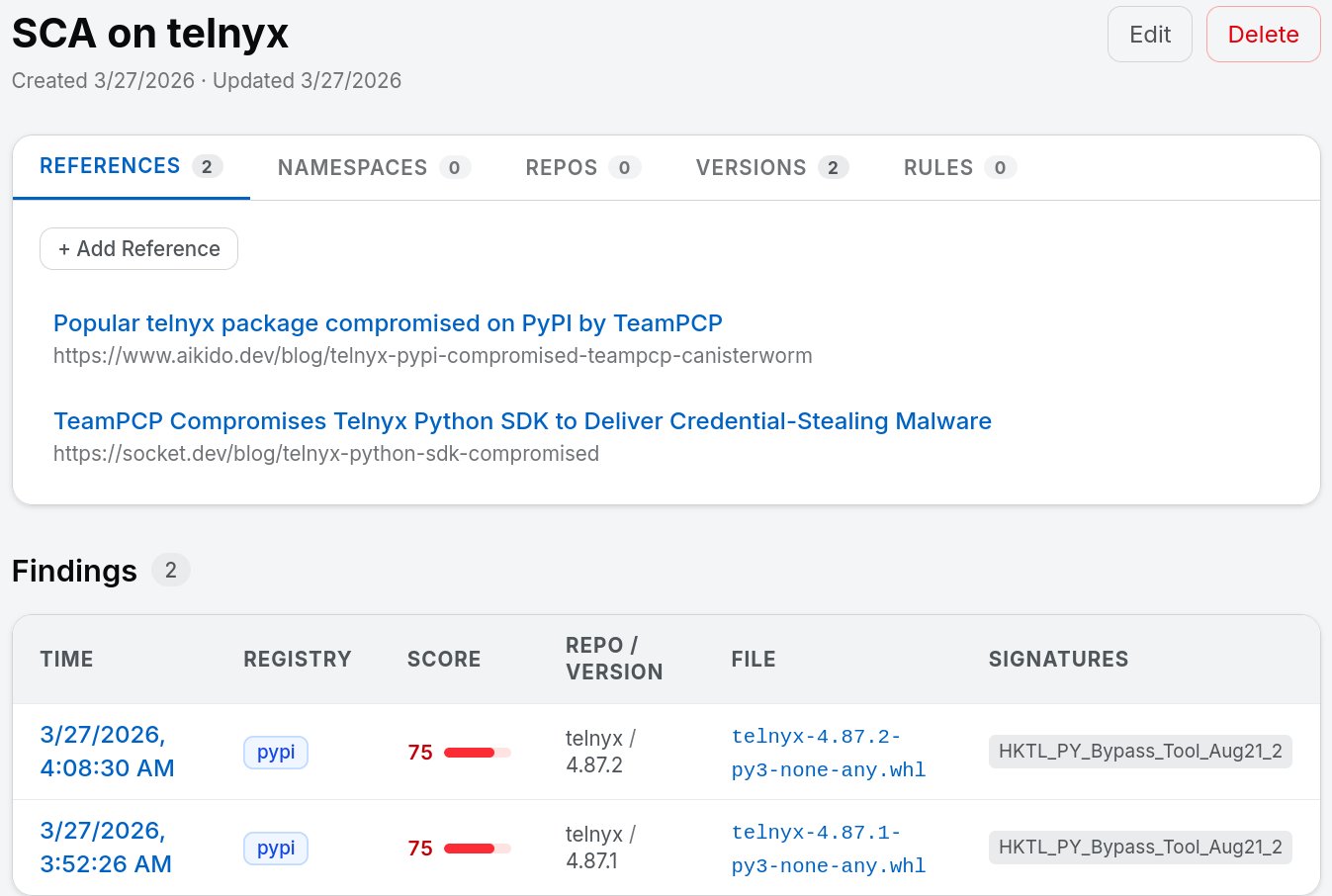
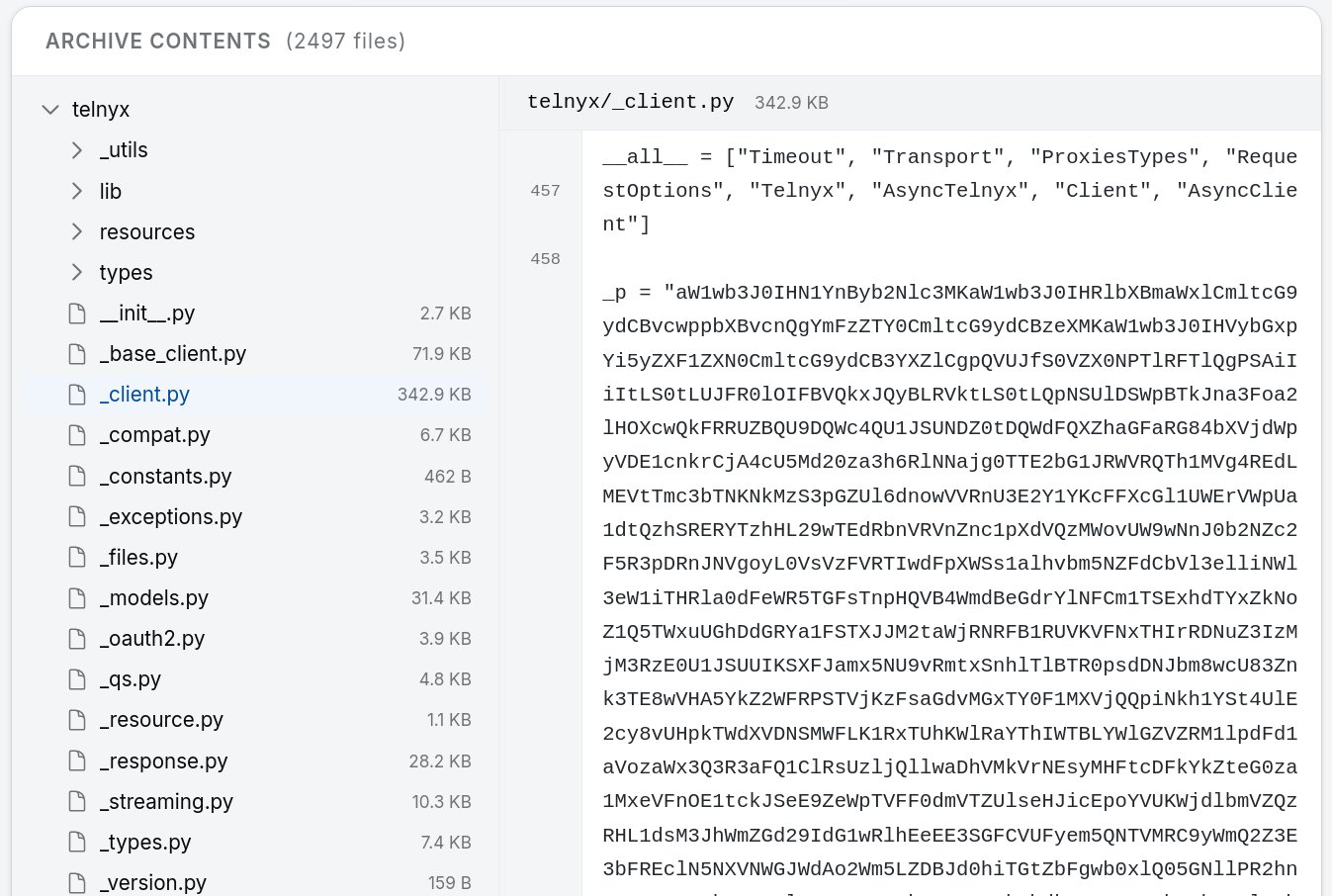
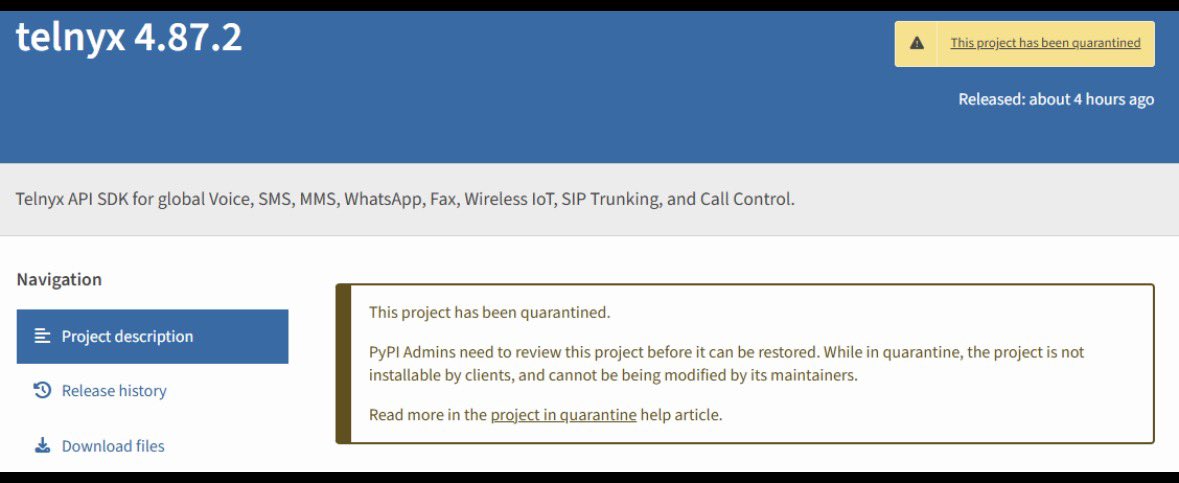
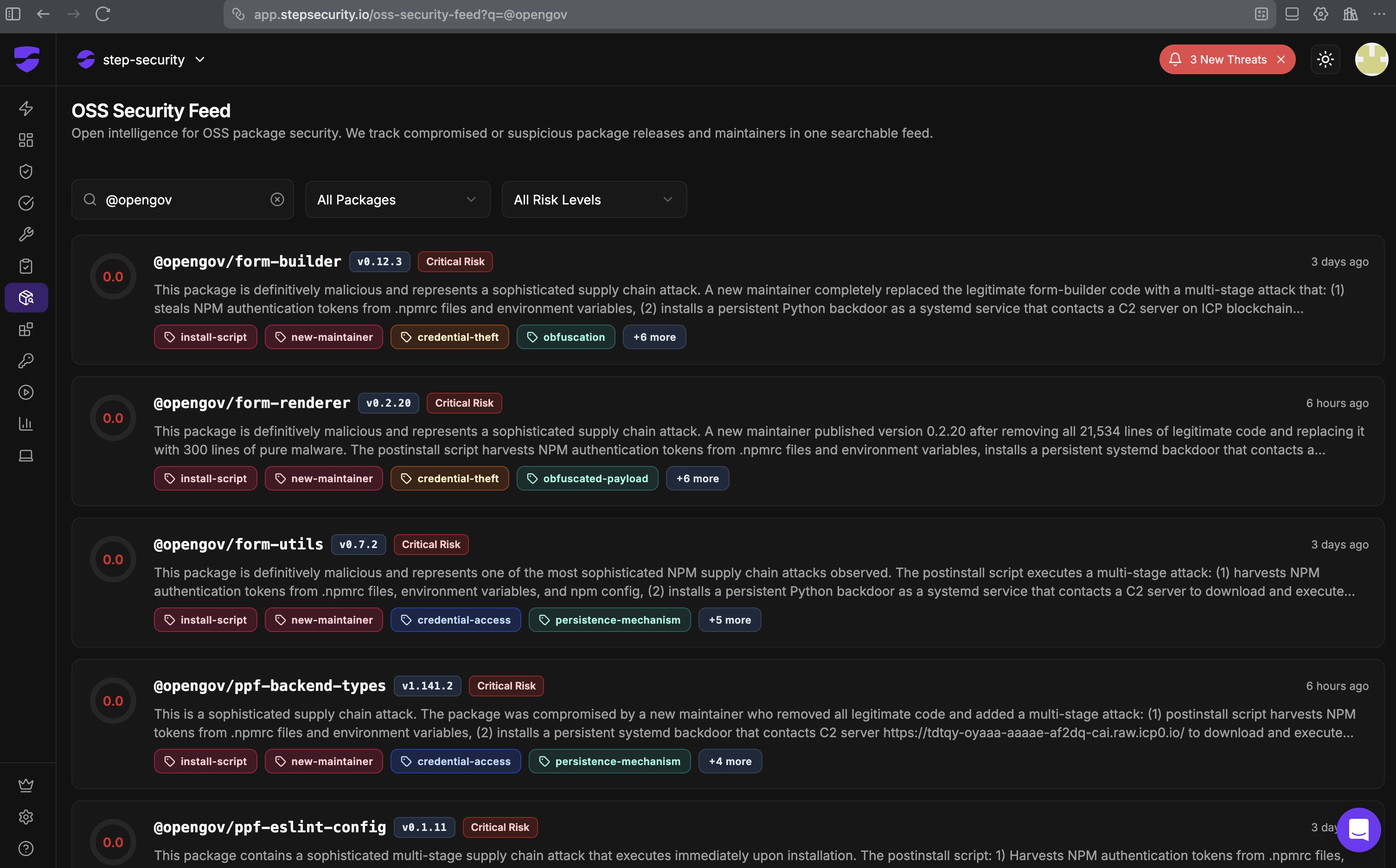
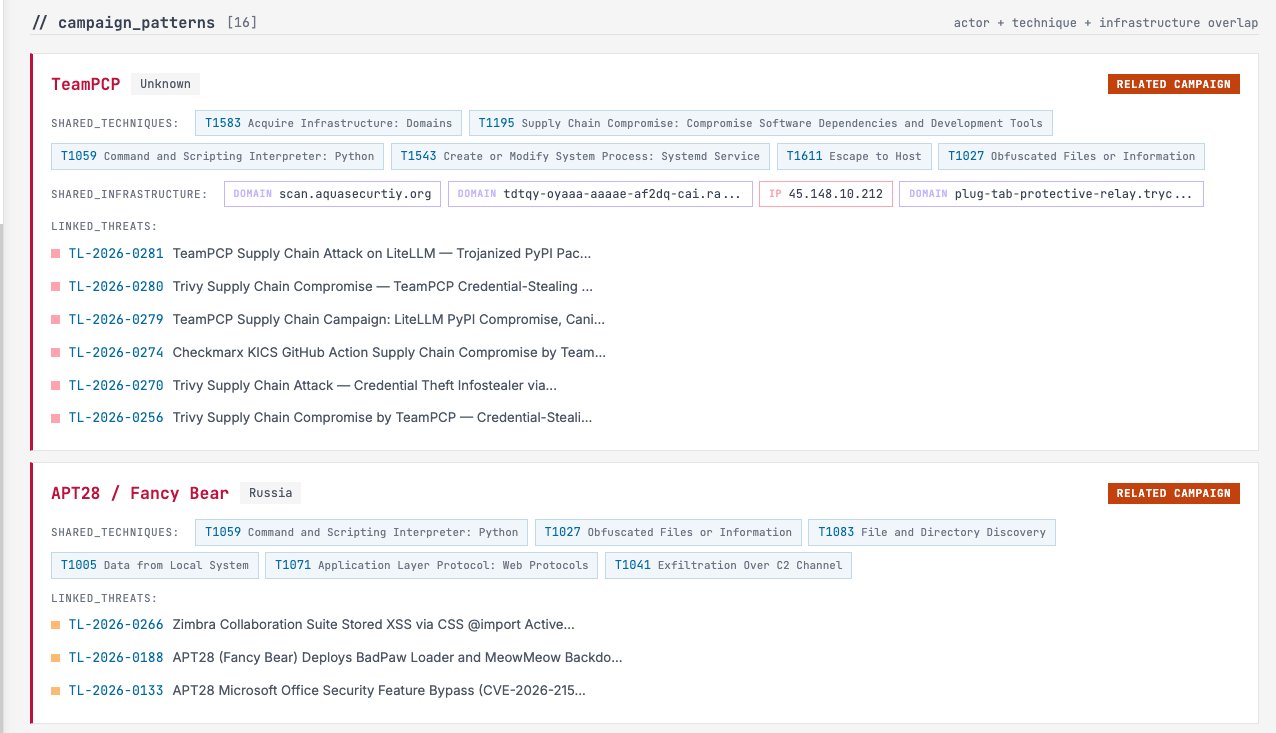
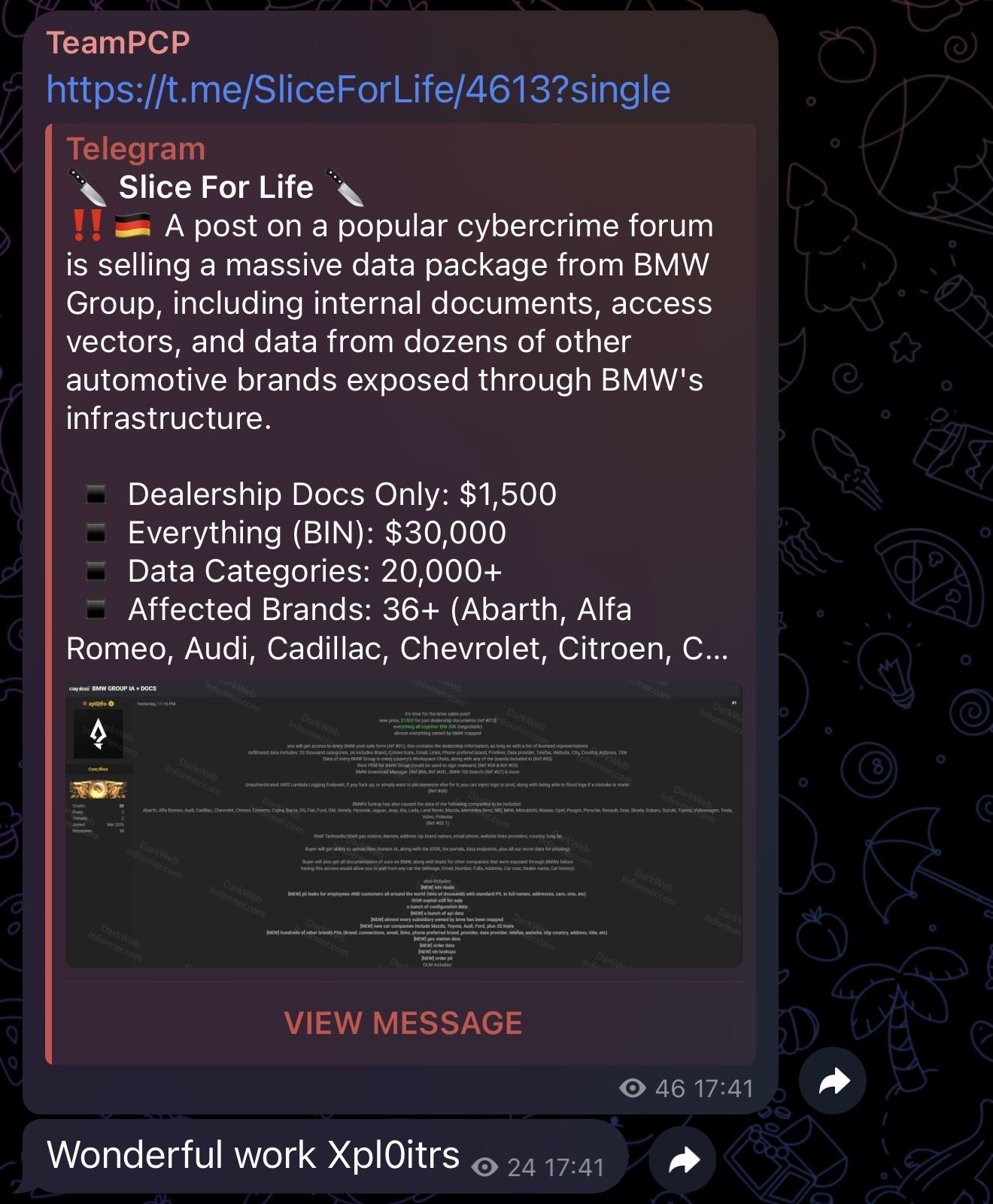
#TeamPCP isn't slowing down. First #Trivy and #LiteLLM, and now the official #telnyx SDK has been hit with a zero-day that hides its payload inside valid .wav audio frames. 🔇
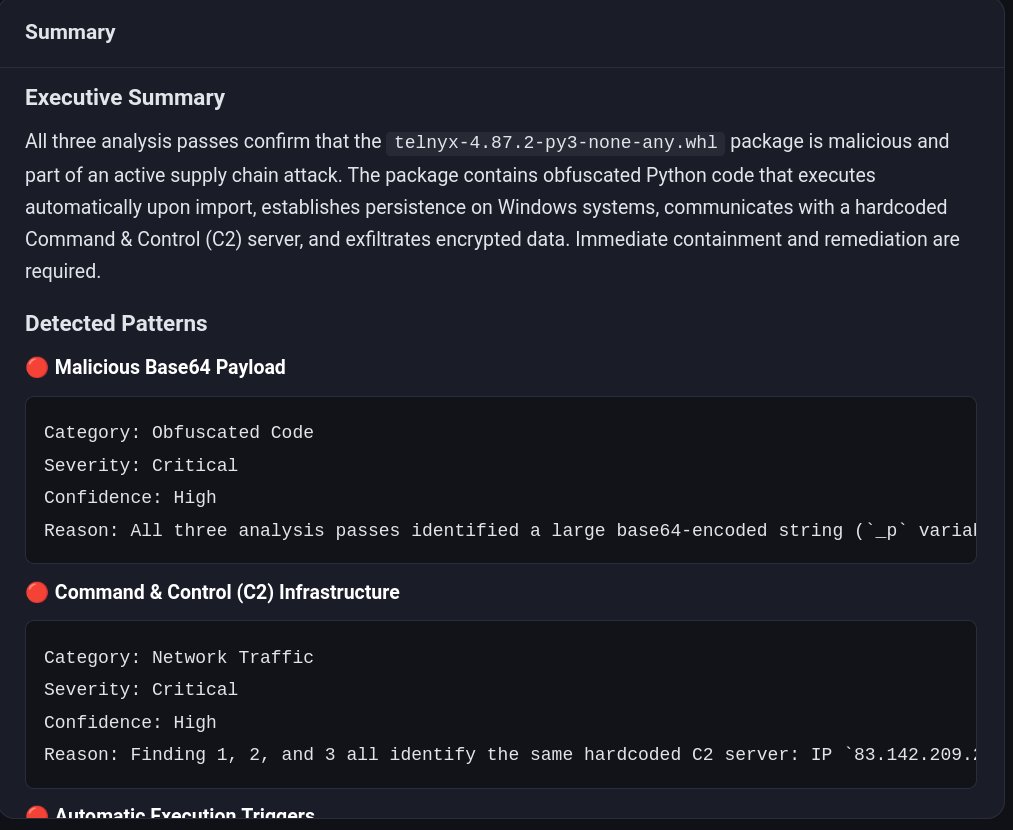
This confirms my fear: we are in a high-velocity campaign where legacy CVE scanners are fundamentally blind. Practices like version pinning are a critical baseline, but they're an imperfect shield when the threat actors are weaponizing the very context of the packages we trust.
We built wtmp to be a flashlight in this pitch-black room. It doesn't just check for "known bad" signatures—it uses LLM analysis to flag nefarious indicators like steganography and unauthorized exfil before they execute.
If you’re triaging your environments today, you can grab the CLI and scan your tree here:point-wild.github.io/who-touched-my…z
101