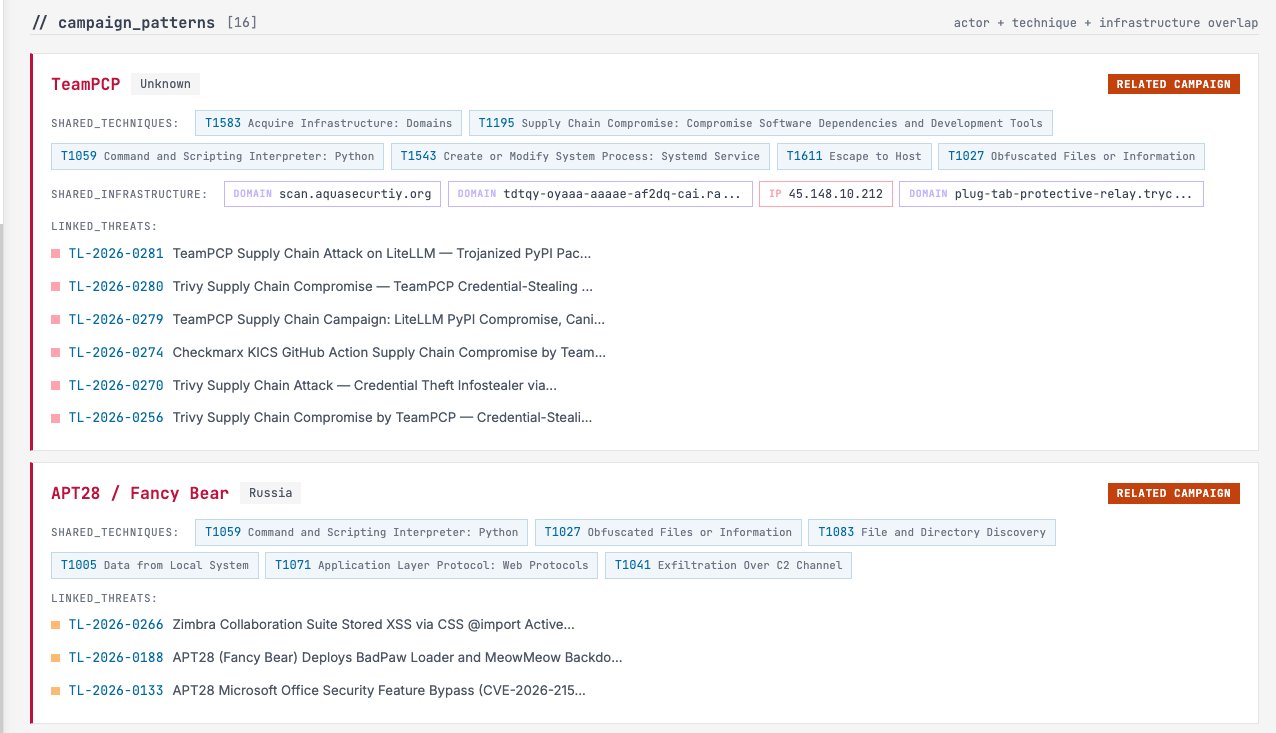
#TeamPCP just partnered with
#Vect ransomware.
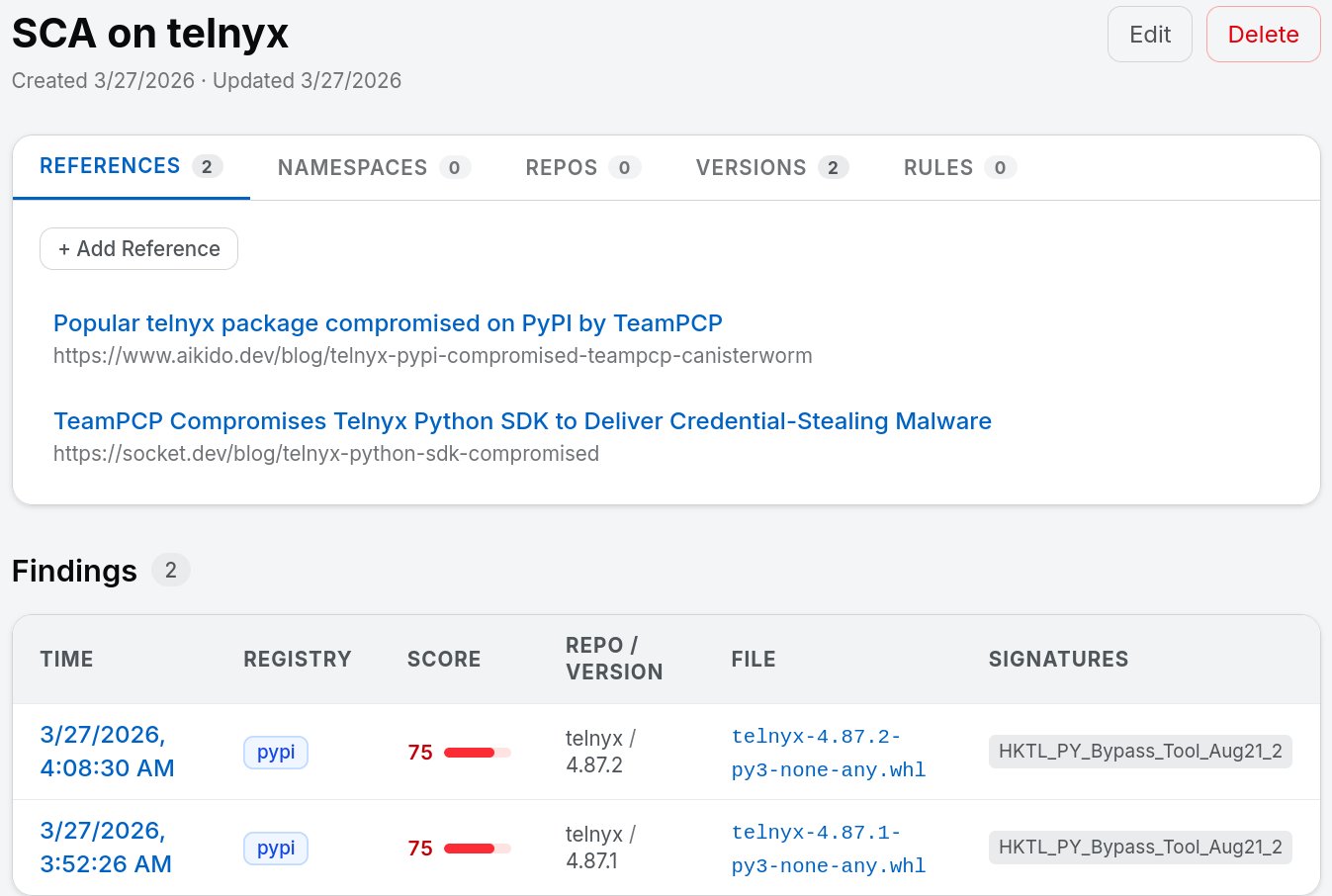
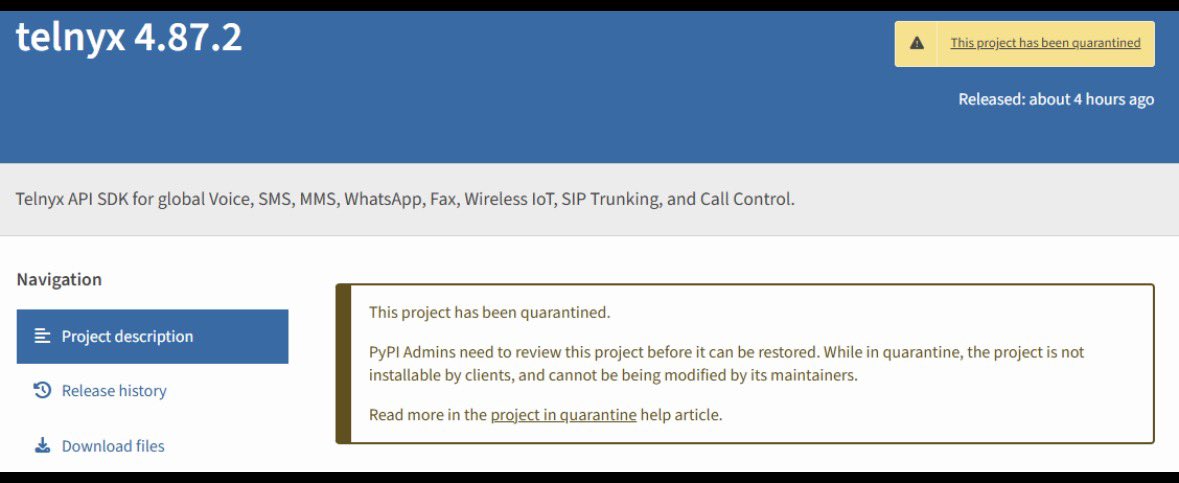
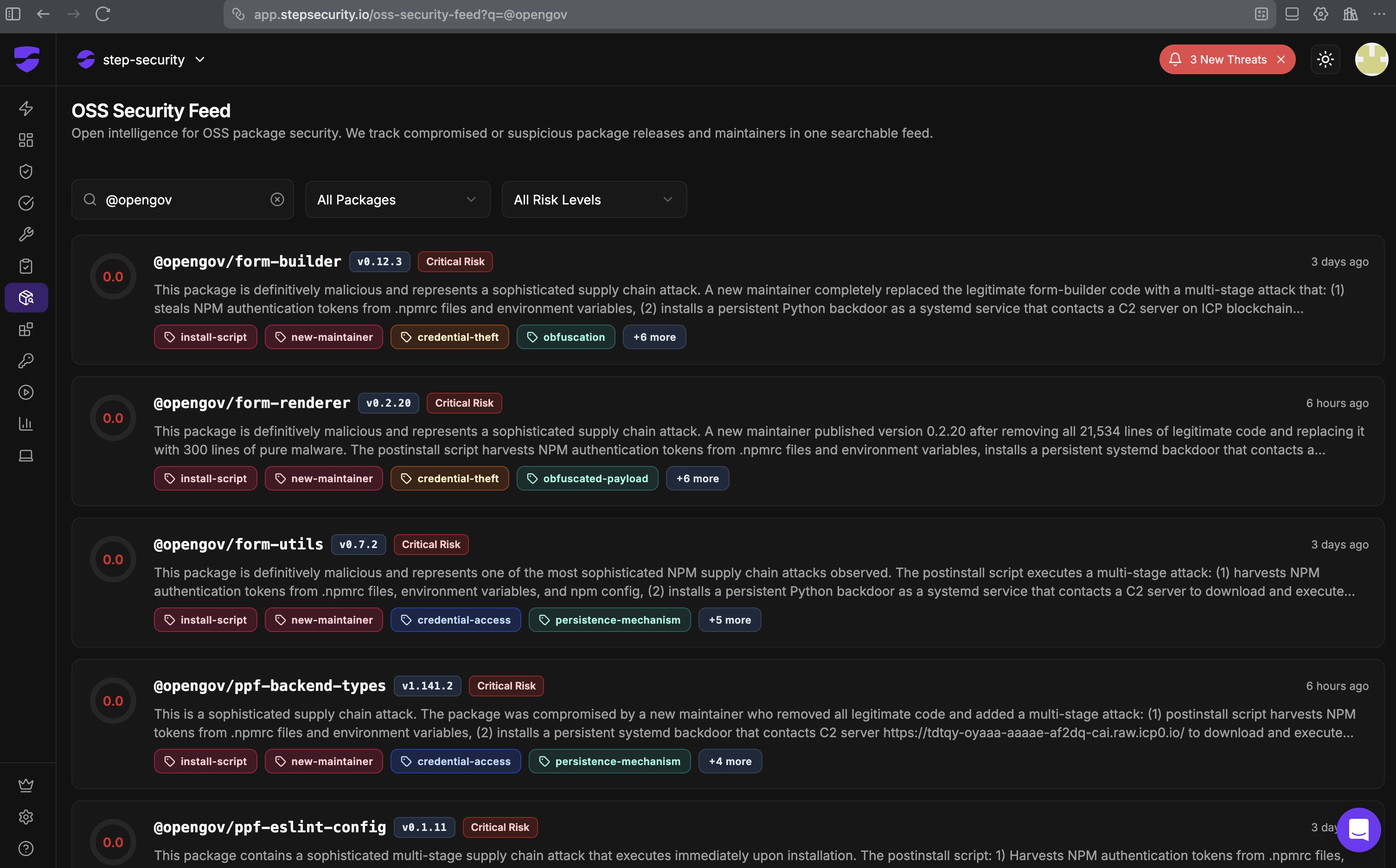
The same group that backdoored $Trivy, hijacked Checkmarx KICS, and trojanized
#LiteLLM on PyPI — a package pulled 3.4M times per day — is now feeding 300GB of stolen credentials into a ransomware-as-a-service pipeline. 80-88% tors.
We tracked the full campaign across 7 threats on Threadlinqs Intelligence:
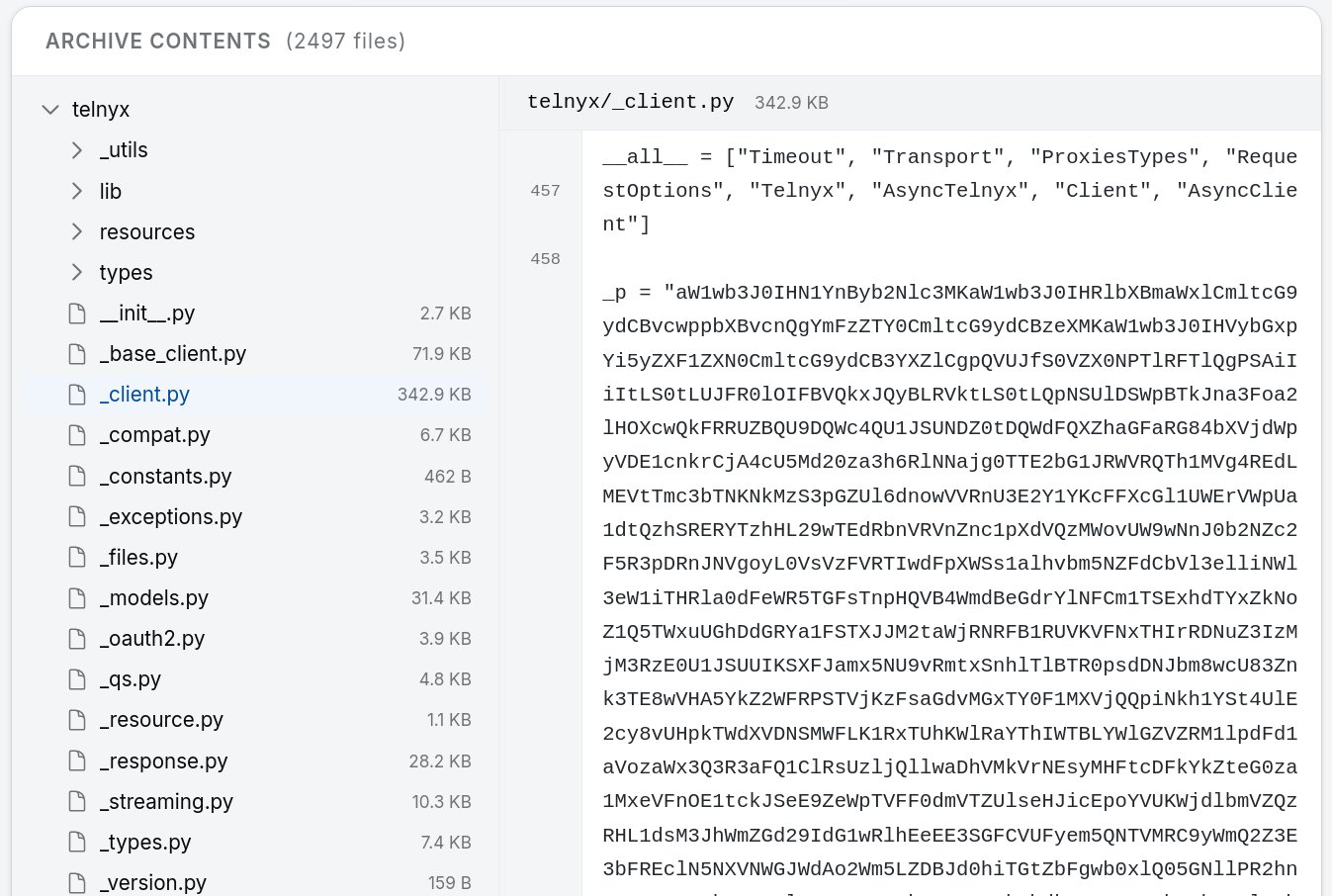
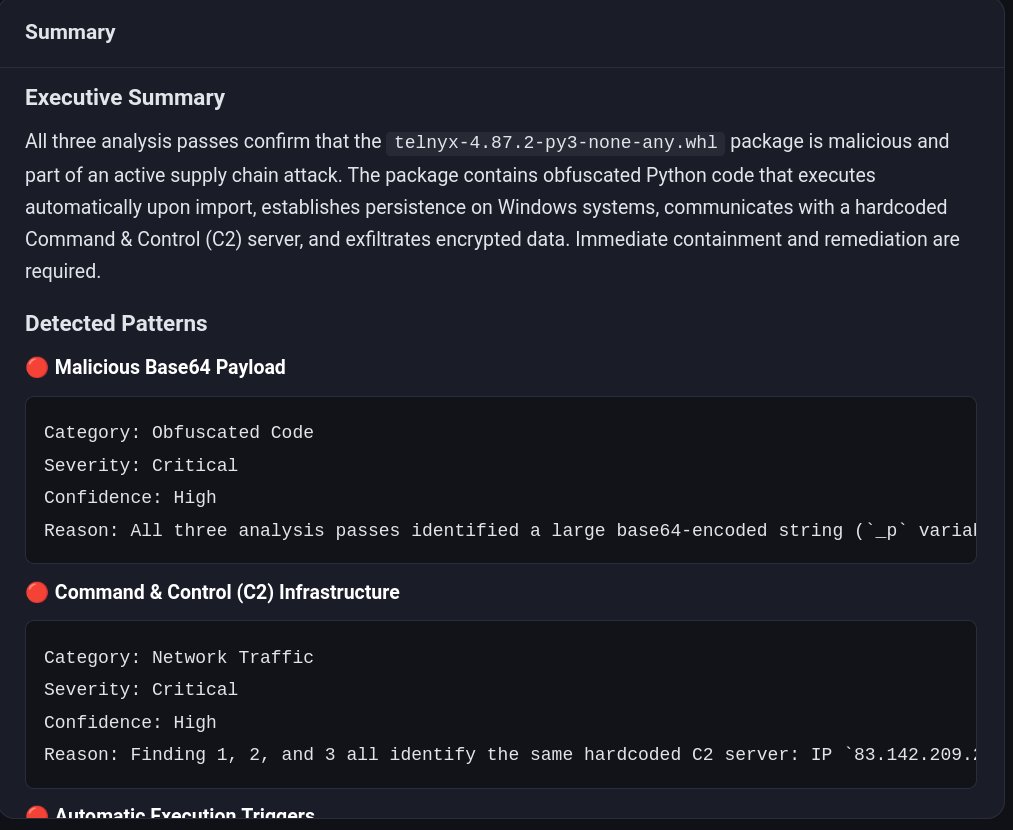
→ .pth file persistence that survives pip uninstall and runs on every Python invocation
→ 332-line credential harvester sweeping AWS, GCP, Azure, K8s, SSH, npm tokens
→ Kubernetes lateral movement via privileged pods in kube-system
→ CanisterWorm — a self-replicating npm worm using blockchain (ICP) as C2
→ 60,000+ compromised servers. 85 MITRE techniques. 63 detections written.
The IOC correlation alone tells the story —
scan.aquasecurtiy.org (the typosquatted domain) links all 7 campaign phases. Same
RSA-4096 key. Same tpcp.tar.gz naming. Same kill-switch logic.
Full deep dive with enriched IOCs, detection rules (SPL/KQL/Sigma):
threadlinqs.com/blog/TL-2026-0…