Organizations often struggle with security due to rogue IT and multiple instances of the same software. #Cybersecurity #ZeroTrust #ITSecurity
2









The Model Context Protocol connects AI agents to enterprise tools — but it ships without authentication, authorization, or audit trails. With 7,000+ exposed servers and a growing list of CVEs, MCP...
From brightbean.xyz
### The "Emergency Brake" for AI AgentsYour AI agents are powerful, but sometimes they need a human. Red Telephone is a plug-and-play MCP server that lets any AI agent pause and ask you a question ...
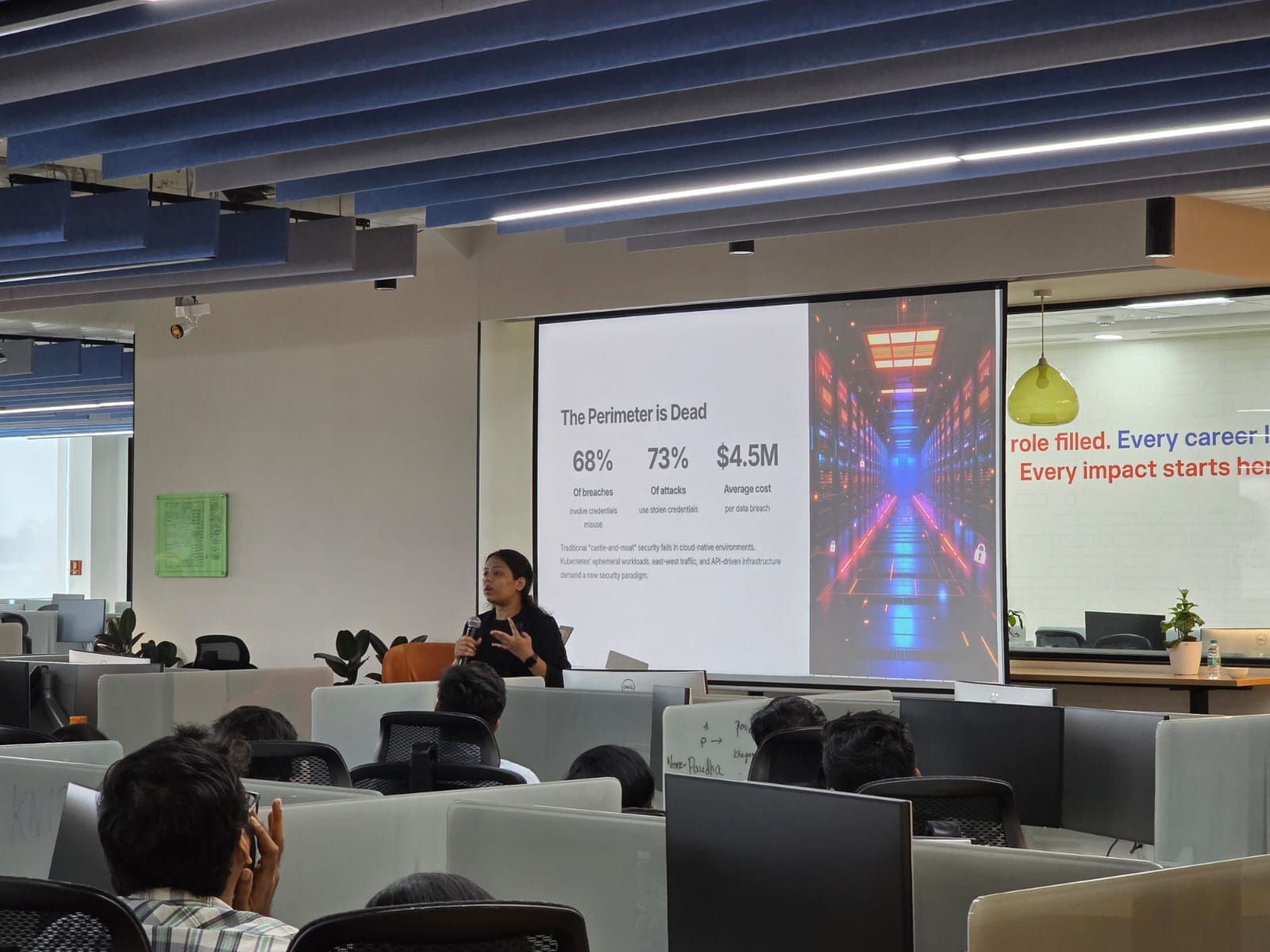
From dantehark.gumroad.comPublished by NSAO | Cybersecurity for Small BusinessesIs your business network truly secure—or does one login unlock everything?Many small businesses still rely on outdated “trust-based” security...
From nsao.com
