Search
This article explains CVE-2020-8561, an unpatchable Kubernetes vulnerability that combines an SSRF vector via ValidatingWebhookConfiguration objects with the API server's profiling endpoints to...
From hendryadrian.comFollow us on Bluesky, Twitter (X), Mastodon and Facebook at @Hackread
From hackread.comTrivy supply chain attack pushed malicious Docker images on March 22, enabling credential theft and worm spread, impacting cloud environments.
From thehackernews.comA cyber intrusion attributed to a suspected North Korean threat group reveals how attackers can move from a developer’s personal device to corporate cloud infrastructure, exploiting DevOps workflow…
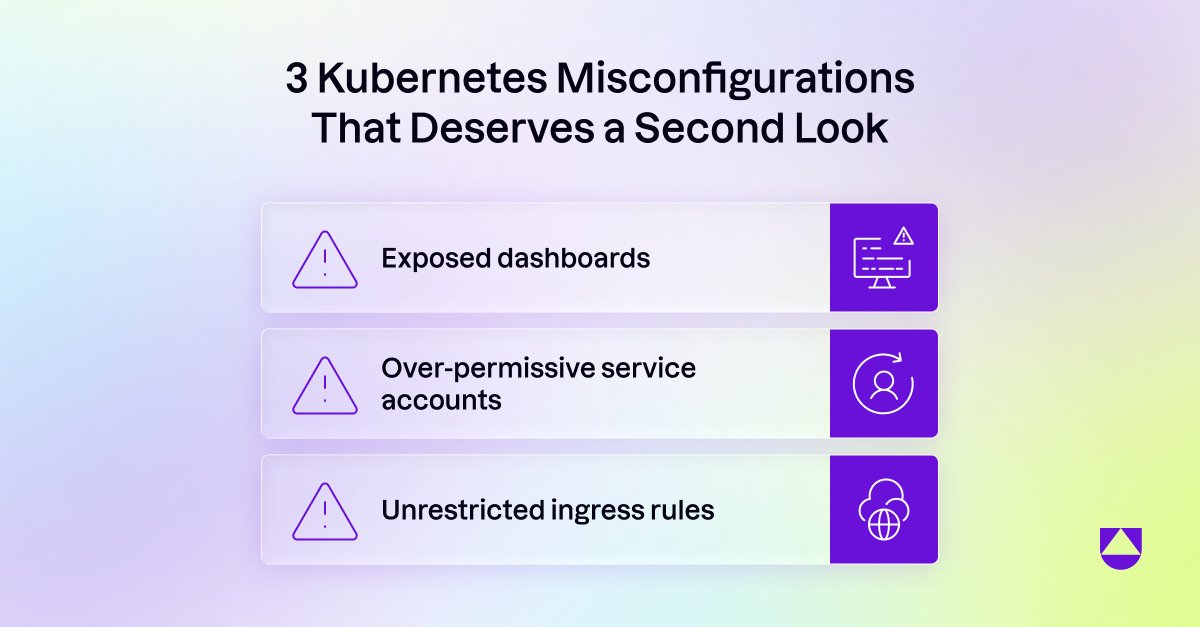
From the420.inRole-Based Access Control (RBAC) stands as a cornerstone for securing and managing access within the Kubernetes ecosystem. Think of Kubernetes as a bustling city, with myriad services, pods, and...
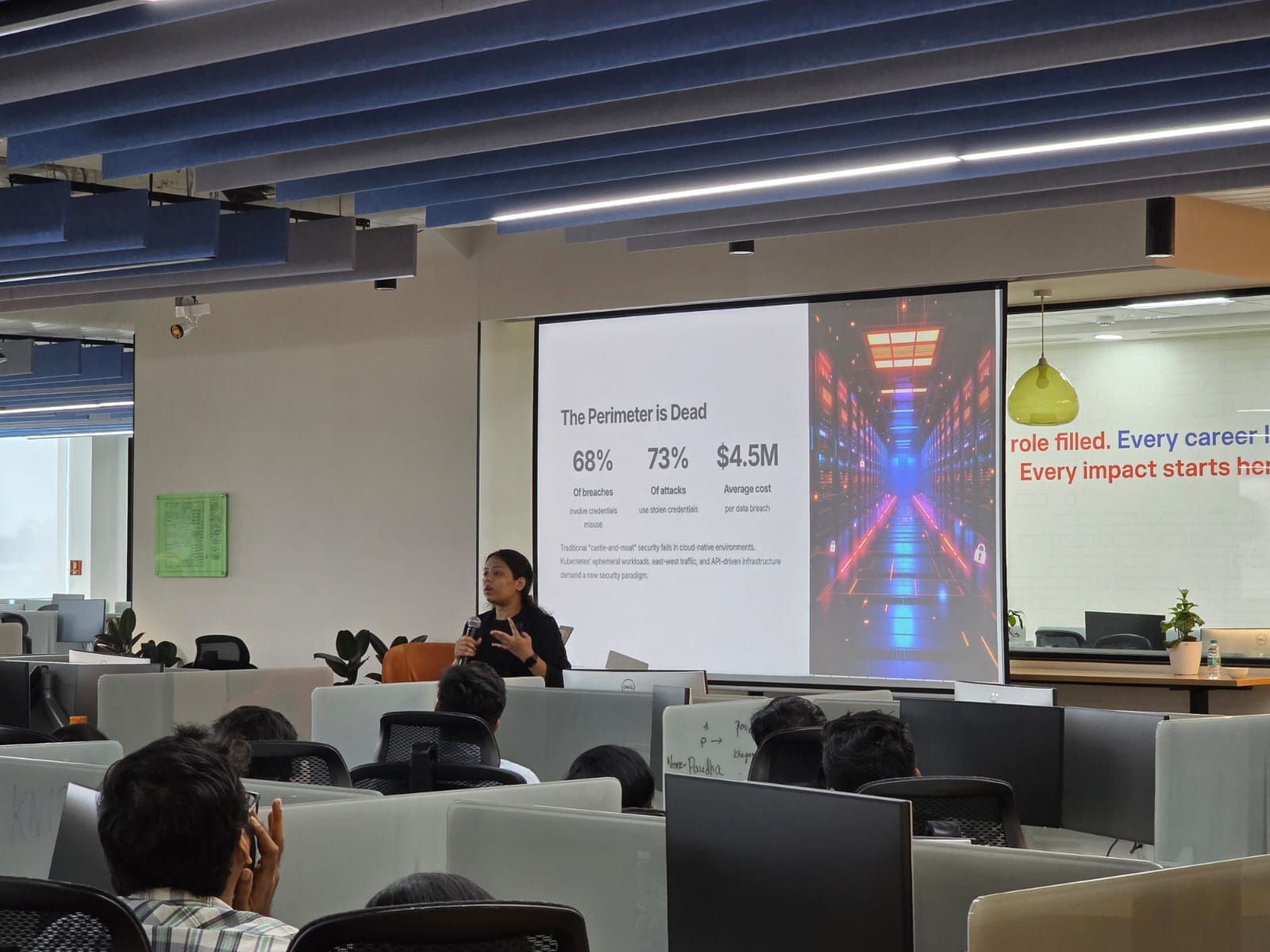
From nivelepsilon.comDiscover how a zero-trust strategy can secure non-human identities in Kubernetes. Protect sensitive data with prevention, detection, and recovery. Know more!
From techdemocracy.com