Search
A collection of independent CTI reports covering active threat campaigns and attacker TTPs. - seraphimdeck/SerapHim-CTI
From github.comIn this blog post, we share our analysis of the StoatWaffle malware newly adopted by WaterPlum
From jp.security.ntt本稿では、WaterPlumが新たに使い始めたStoatWaffleマルウェアについて、解析結果を共有します。
From jp.security.nttIn this blog post, we share our analysis of the StoatWaffle malware newly adopted by WaterPlum
From jp.security.ntt本稿では、WaterPlumが新たに使い始めたStoatWaffleマルウェアについて、解析結果を共有します。
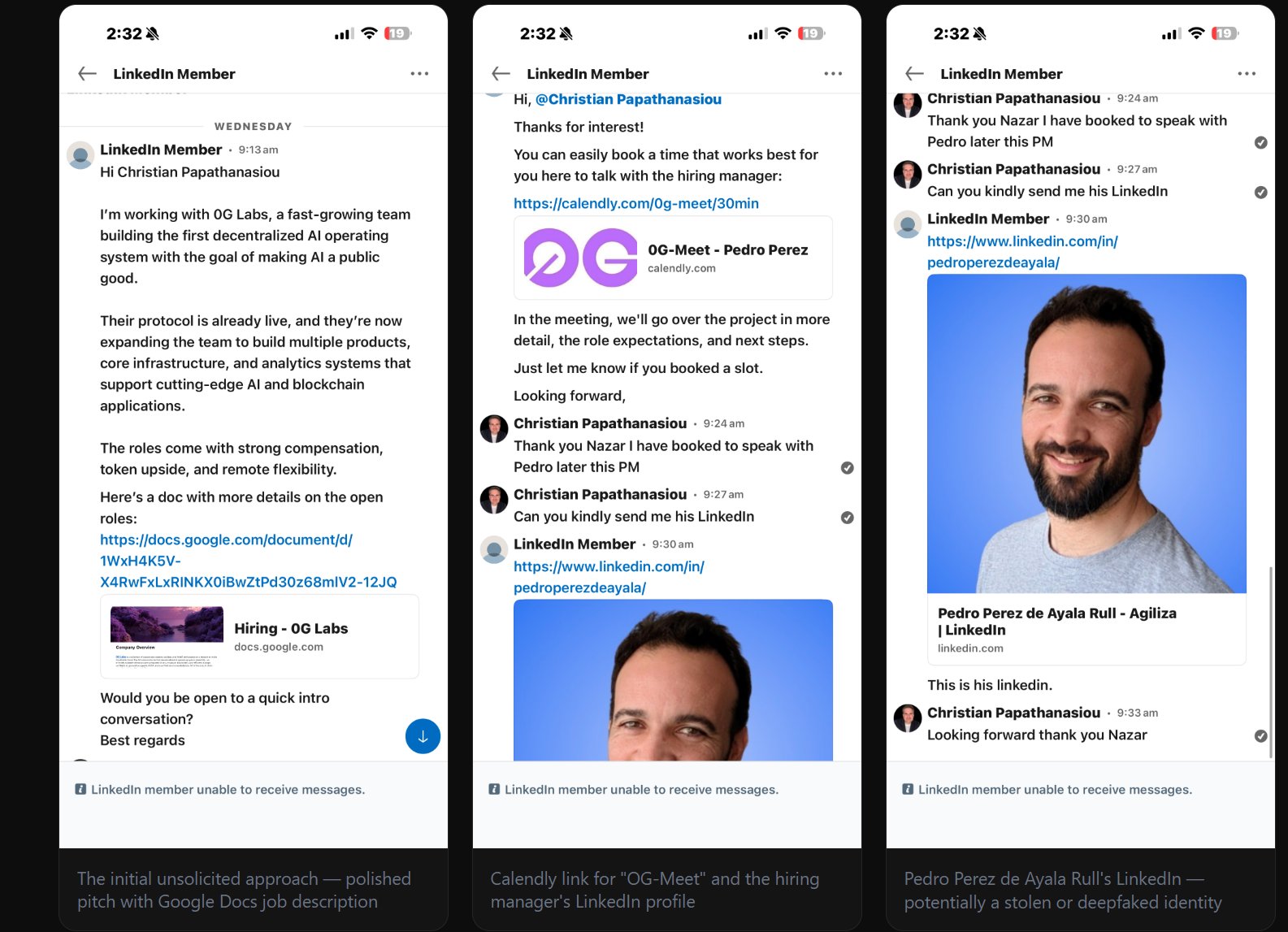
From jp.security.nttThe Contagious Interview campaign weaponizes job recruitment to target developers. Threat actors pose as recruiters from crypto and AI companies and deliver backdoors such as OtterCookie and Flexib...
From microsoft.comAllSecure's CEO was personally targeted by North Korea's Lazarus Group via LinkedIn with a fake job interview. Instead of falling for it, he trapped them — and reverse-engineered every stage of their...
From allsecure.ioAnalysis of the Contagious Interview campaign’s WeaselStore malware chain, including PylangGhost and GolangGhost deployment techniques, VS Code task abuse, and practical detection and mitigation...
From abstract.securitySocket uncovered 26 malicious npm packages tied to North Korea's Contagious Interview campaign, retrieving a live 9-module infostealer and RAT from th...
From socket.devASTRO tracks fresh Contagious Interview evolutions: shortened URLs masking Vercel infrastructure, NVIDIA-impersonating GitHub Gists, and Google Drive payload delivery with a virus-scan bypass....
From abstract.security(Presented by TLPBLACK: High-fidelity threat intelligence and research tools for modern security teams. From curated Passive DNS and real-time C2 monitoring to actionable IOC feeds […]
From securityconversations.comGitLab reveals how North Korean fake IT workers use 'Contagious Interview' scams to bypass hiring, steal data, and hijack executive digital identities.
From securityonline.info