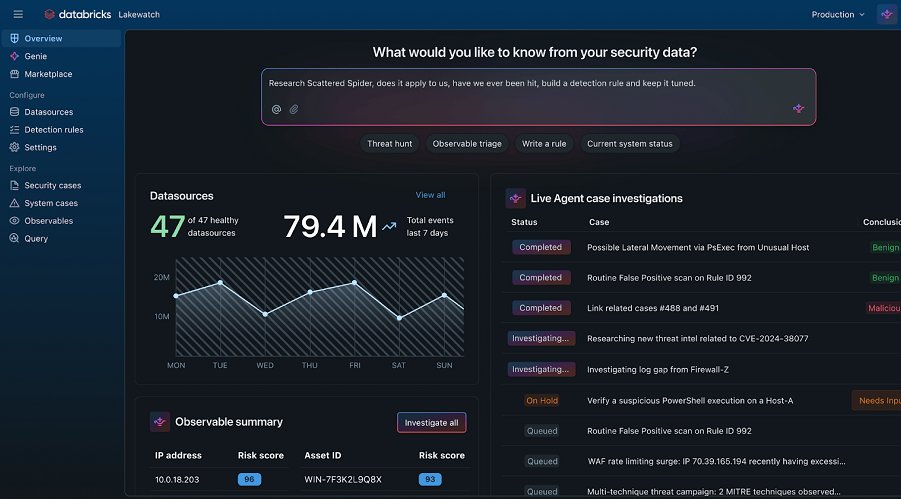
The average dwell time for a breach is 207 days. Attackers are sitting in networks for 6 months because standard SIEMs only flag what they already know. 🥷
I built Phish-Slayer to stop reacting, and start predicting. #SOC #IncidentResponse #SIEM
1
1