
Search
Microsoft Entra IDのアプリ同意(OAuth consent)を統制して、Shadow ITと監査対応を同時に楽にする(情シス向け)※本記事は一般的な情報提供を目的としており、個別案件の法的助言・紛争対応・代理交渉等を行うものではありません。必要に応じて弁護士等の専門家と連携してご検討ください。1. 情シスが一番怖いのは「侵入」より“正規の同意”で権限が増えることいまの攻撃は...
From shizuoka-yamazaki-jimusho.com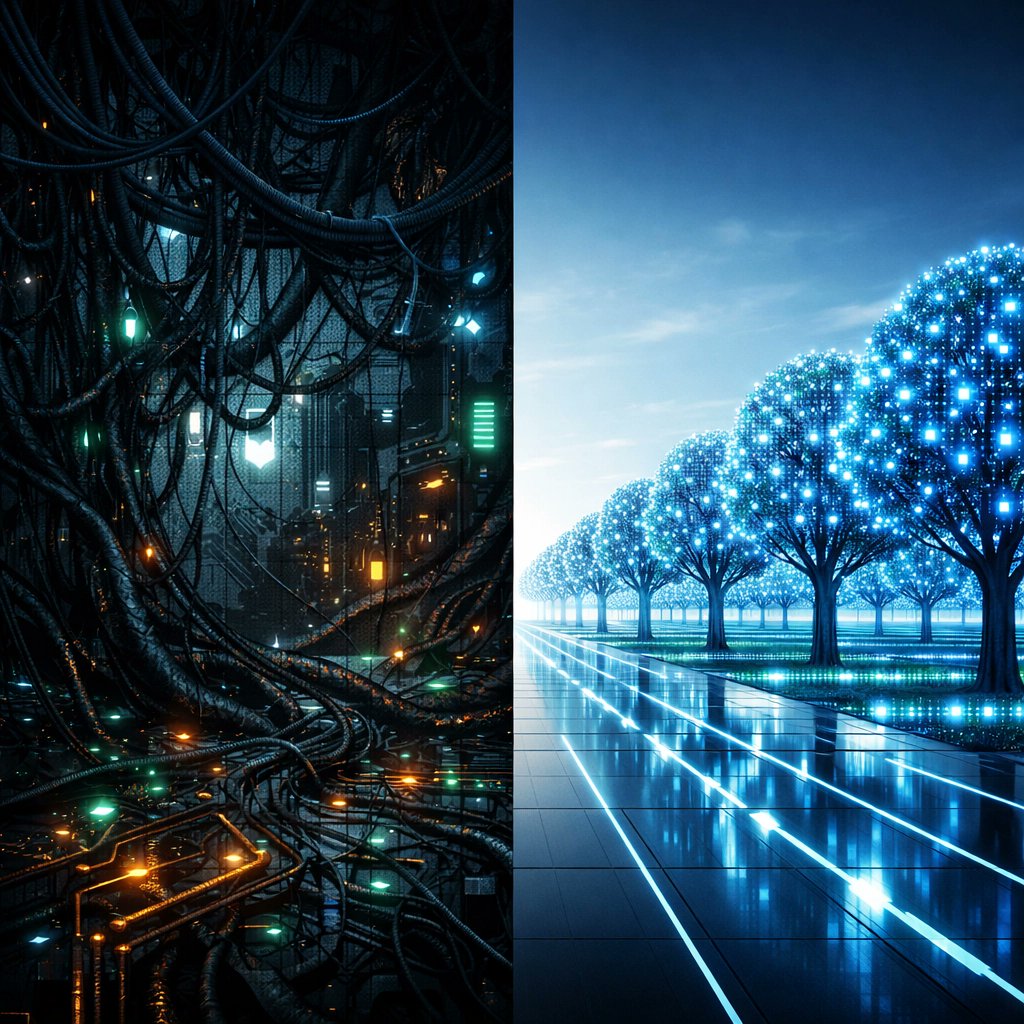






Low-code shadow IT can weaken process governance, accountability, and decision rights. Learn how to manage low-code platform risks with stronger governance.
From panorama-consulting.comIn cybersecurity, a database exposure is a critical security flaw in which sensitive database files, records, or access credentials become accessible to unauthorized individuals or the public...
From threatngsecurity.com


Threat-Informed External Attack Surface Management (EASM) is an advanced cybersecurity discipline that combines continuous internet-facing asset discovery with real-time threat intelligence. Instead...
From threatngsecurity.comThreat-Informed External Attack Surface Management (EASM) is an advanced cybersecurity discipline that combines continuous internet-facing asset discovery with real-time threat intelligence. Instead...
From threatngsecurity.com