🚀 Together, we continue to promote cyber awareness and build a secure digital future.
#CyberJagruktaDivas #CyberSecurity #SecureDesign #ApplicationSecurity #PasswordManagement #CyberAwareness #Workshop #SRMIST #DigitalSecurity
10





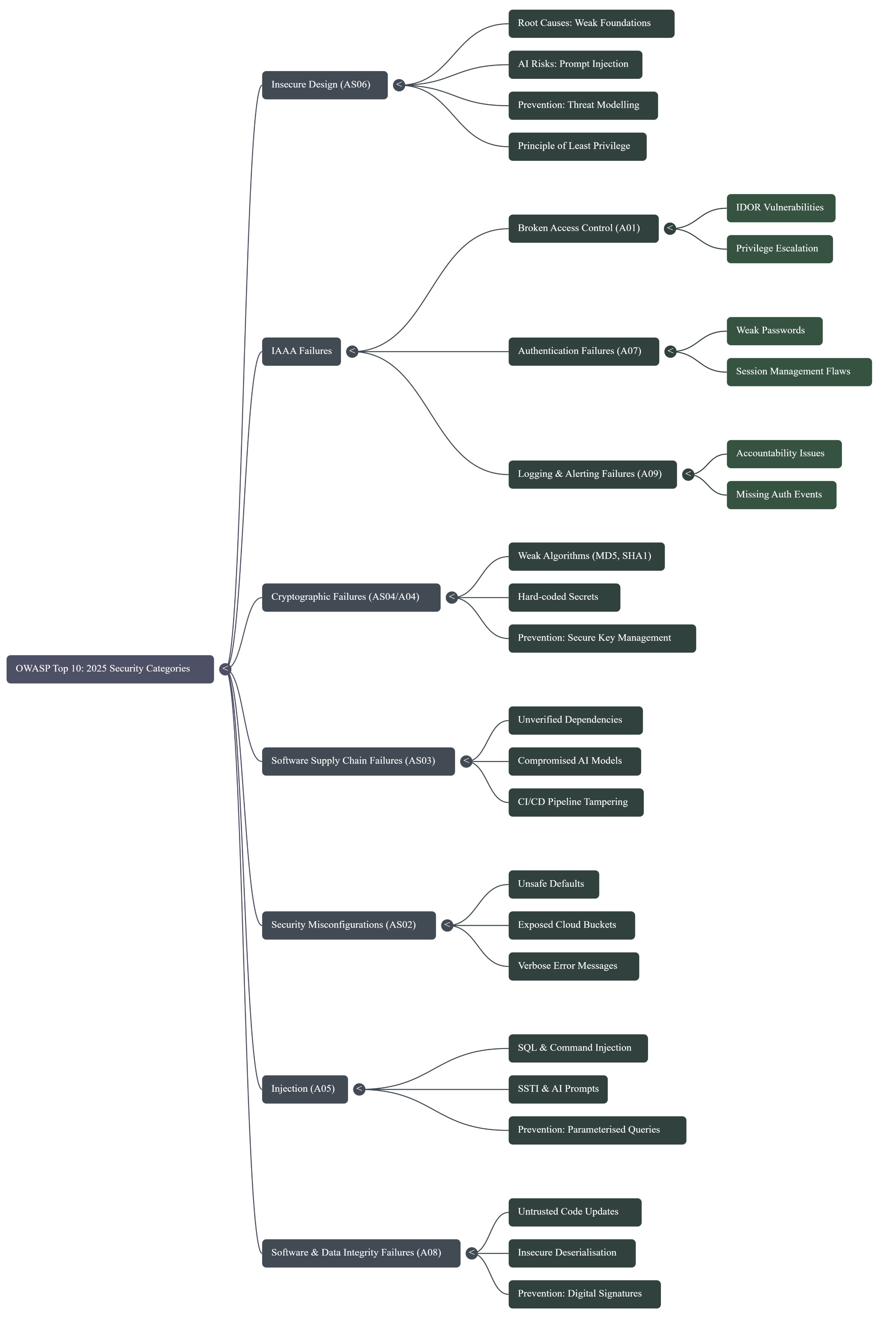
PASTA application threat modeling gives tactical steps to mitigate cybersecurity risks. We analyze attacks that can exploit vulnerabilities.
From versprite.com