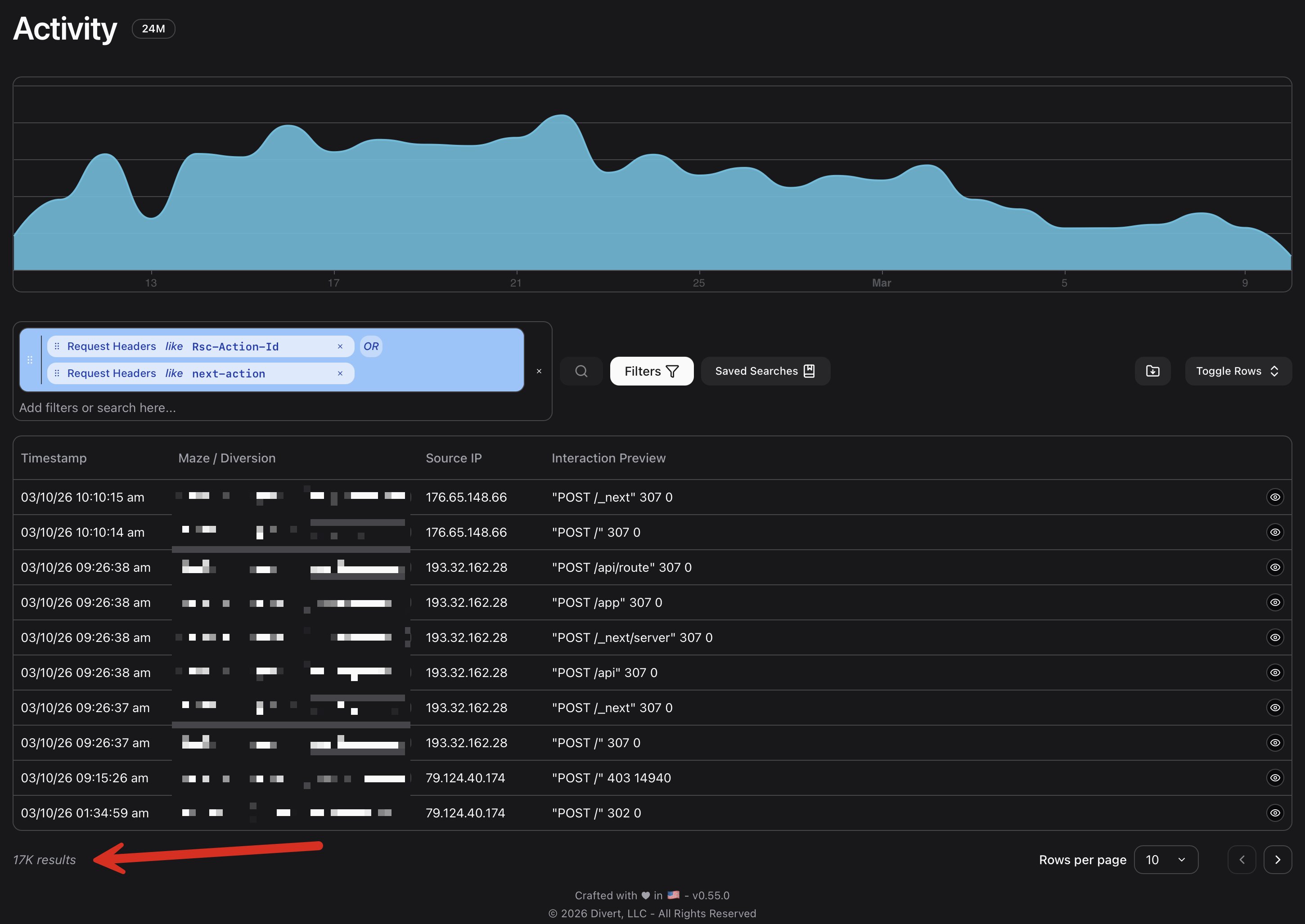
Search
「WAFを導入しているから安心」という常識が今、音を立てて崩れている。2025年末に発生した「React2Shell」攻撃は、WAFの仕様上の死角を突く巧妙な回避手法を顕在化させた。生成AIを駆使し、自律的に攻撃パターンを変化させるAIエージェントの脅威も現実のものとなりつつある。高度化する「WAF回避」の猛攻を前に、WAFの新要件を解き明かす。
From atmarkit.itmedia.co.jp


Google's latest cloud threat report shows bug exploitation has overtaken credential theft as the primary entry point for attackers.
From ghacks.netHackers linked to North Korea targeted crypto firms using React2Shell exploits and stolen AWS credentials, exposing code, secrets, and cloud infrastructure.
From cryptofrontnews.comCtrl-Alt-Intel exposes a suspected DPRK campaign using an 'Amazon Kill Chain' and React2Shell to systematically breach crypto exchanges and steal code.
From securityonline.infoReact2Shell vulnerability CVE-2025-55182 is actively exploited to deploy Linux malware, run commands, and steal cloud credentials at scale.
From thehackernews.comA suspected DPRK-associated actor compromises crypto orgs, pillaging cloud environments, stealing proprietary exchange software and source code.
From ctrlaltintel.com
Step by step guide for testing the React2Shell critical RCE vulnerabilitiy using SmartScanner GUI and command line interface. Test single or a list of URLs for Next.Js react2shell vulerability.
From thesmartscanner.comExplore the latest news and expert commentary on Application Security, brought to you by the editors of Dark Reading
From darkreading.com