#GoPlusSecurity ( $GPS ) -
#Explainer
💡 What is GoPlusSecurity ( $GPS )?
GoPlus Security is a leading Web3 security infrastructure project that provides a decentralized security layer for users, wallets, DeFi protocols, and blockchains. It focuses on real-time scam detection,nsaction protection across the blockchain ecosystem, aiming to make Web3 security accessible to everyone while combating threats such as phishing, rug pulls, and malicious smart contracts.
The project positions itself as the “security layer” of Web3 — similar to how Chainlink serves as an oracle layer for data, but instead focused on risk and security intelligence. GoPlus has built an ecosystem of tools and services that protect millions of wallets and secure billions of blockchain transactions.
The native token $GPS is central to this ecosystem and is used for security service payments, staking, governance, and incentivizing contributors who provide security data.
#CryptoEcosystem
⚙️ How does GoPlusSecurity work?
The GoPlus ecosystem consists of multiple products and solutions that work together to deliver comprehensive blockchain security:
🔸 GoPlus App
A personal security hub (available as a browser extension and mobile app) offering wallet scans, transaction simulation, and real-time alerts that warn users about potential risks before interacting with smart contracts or transactions.
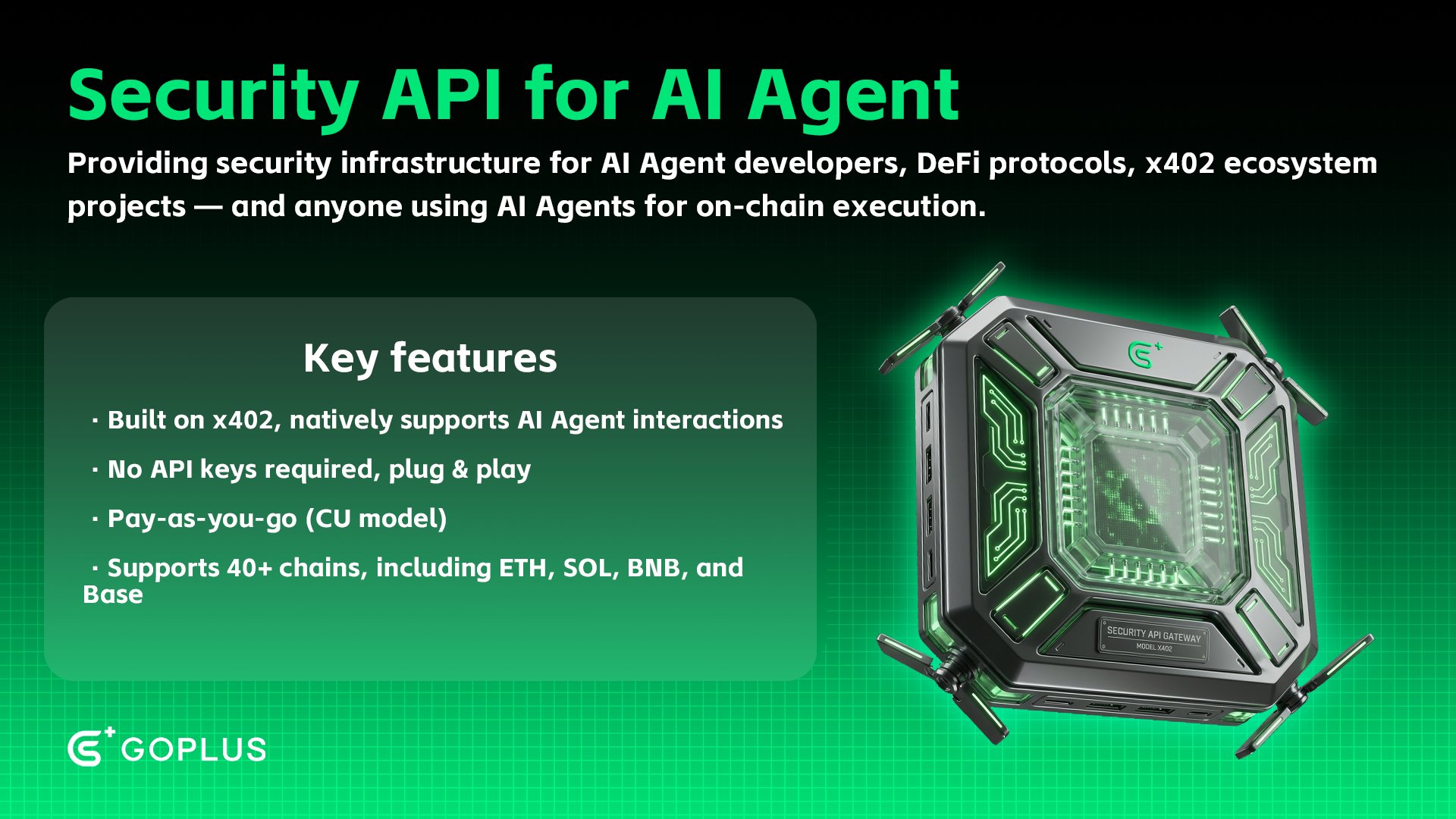
🔸 Security APIs
AI-powered tools and APIs integrated by projects, wallets, and chains to detect risks such as malicious token contracts, NFT fraud, and suspicious addresses.
🔸 GoPlus Security Module (GSM)
A chain-native security layer — effectively an on-chain firewall — that can be directly integrated into blockchains to enforce security rules and perform risk analysis within transaction flows.
🔸 SecWares & SecNet
A decentralized network of node operators and data providers who contribute real-time security intelligence, enabling continuous threat detection across the ecosyst
em.
#BlockchainInnovation
🪙 The role of $GPS
The $GPS token serves multiple core functions within the GoPlus ecosystem:
🔸 Payments
$GPS is used to pay for security services, API usage, and advanced risk analysis tools within the network.
🔸 Staking
Node operators, data providers, and AVS operators stake $GPS to earn rewards while contributing to the security and reliability of the network.
🔸 Governance
Token holders participate in governance through the Governance Portal, voting on proposals, upgrades, and ecosystem strategies.
🔸 Incentives
Contributors who provide security data, alerts, and node services are rewarded in $GPS, encouraging active participation and network
growth.
#Tokenomics
🛠️ Key characteristics:
🔸 Total supply: 10 billion $GPS
🔸 Circulating supply: Approximately 44% of the total supply
🔸 Utility: Payments for security services, staking, governance, and ecosystem incentives
🔸 Vesting: Team and early investors follow vesting schedules with cliff periods and linear unlocks to ensure long-term alignment
🔸 Incentives: A significant portion of the supply is allocated to community growth, ecosystem development, and rewards for security dat
a contributors
#BlockchainProgress
📜 History and development:
The evolution of GoPlusSecurity reflects a phased rollout of security products and decentralized infrastructure:
2023: Introduction of real-time security alerts and early app development
2024: Launch of decentralized security tools and initial API integrations
2025: Official $GPS token launch, activation of staking mechanisms, and release of the Governance Portal
2026: Expansion of GSM across multiple blockchains and scaling of the SecNet node network
The team continues to focus on innovation and the expansion of decentralized security infrastructure for Web3, with strong emphasis on AI-driven risk analysis and de
centralization.
#CryptoHistory
💸 Market and user information:
GoPlus Security serves both individual users and institutional projects requiring real-time security solutions. The GoPlus App protects millions of wallets and processes large volumes of transactions daily to identify risks befor
e damage occurs.
#MarketAnalysis
✅ Advantages of GoPlusSecurity:
🔸 Strong focus on real-time security and risk detection
🔸 Decentralized network of data providers and node operators
🔸 Multi-chain support for security services
🔸 Incentive-driven participation model
🔸 Community-based
governance structure
#DeFiApplications
⚠️ Challenges and risks:
🔸 Intense competition from other blockchain security and risk analysis projects
🔸 Technical complexity of integrating with protocols and blockchains
🔸 Dependence on broad adoption for maximum effectiveness
🔸 Market uncertainty and vol
atility may impact growth
#CryptoChallenges
🛠️ Use cases and adoption:
GoPlusSecurity offers a wide range of practical use cases:
🔸 Wallet protection: Safeguarding users against scams and malicious interactions
🔸 Protocol integrations: Embedding security APIs into DeFi protocols for risk monitoring
🔸 Chain integrations: Providing on-chain security via GSM across multiple blockchains
🔸 Decentralized security networks: Collaborative threat intelligence through nod
e operators and data providers
#DeFiAdoption
📊 Network value and adoption:
While market speculation often focuses on price action, the core value of GoPlusSecurity lies in its security infrastructure, adoption by wallets and protocols, and the growing network of contributors supplying
real-time threat intelligence.
#MarketVolatility
🔮 Future outlook:
The future of GoPlusSecurity centers on deeper decentralization, expanded chain integrations, growth of the SecNet network, and continuous improvement of AI-driven security tools. Key growth drivers include:
🔸 Expansion of GSM to 30+ blockchains
🔸 Scaling of the node operator and data provider network
🔸 Strategic partnerships with wallets and DeFi protocols
🔸 Increasing deman
d for security solutions across Web3
#DeFiFuture
🎯 Conclusion:
GoPlusSecurity ( $GPS ) is an innovative Web3 security project focused on delivering a decentralized security layer for users, wallets, protocols, and blockchains. Through products like the GoPlus App, Security APIs, and the GoPlus Security Module, the ecosystem enables real-time protection and risk detection.
By combining advanced technology with community-driven participation and incentive mechanisms, GoPlusSecurity positions itself as a critical infrastructure provider within Web3 security. While adoption and competition remain challenges, the project continues to strengthen its role as a foundational security
layer for the decentr
alized internet
altcoinpedia.notion.site/goplus-securit…� #Click2DYOR 👇
https://t.co/TP8XFKmaSu
────────────────────────────
📚 1Click2DYOR – Do your own homework!
────────────────────────────
Do you want to dig deeper into your favorite altcoin?
On our AltcoinPedia Notion page, you’ll find everything you need:
🔸 Current roadmap (NL & EN)
🔸 Exchanges where it is listed
🔸 Fundamental information (tokenomics, team, use-case)
🔸 Detailed explainer (NL & EN)
🔸 Official links (website, whitepaper, socials)
altcoinpedia.notion.site explained + roadmaps
👉 https://t.co/V2lz8hAgp1 👈
─────────────
⚠️ Important note:
─────────────
🔹 This post is purely for educational purposes and does not constitute financial advice or an investment recommendation.
🔹 Always do your own research before investing in cryptocurrencies.
🔹 Cryptocurrencies are highly volatile – only invest money you are willing to lose.
──────────
👇Follow us👇
──────────
🚨 Follow @CryptoJournaal – the place for independent crypto information:
📰 News | 📊 Facts | 🧠 Backgrounds | 🎓 Education
💬 No sponsored tokens
❌ No paid advertisements
📜 Fully MiCAR-compliant
🔍 Always k
t.me/+rzO9yxnGyUxhZ…─────
📲 Join via:
────────
💬 Telegram: h
x.com/i/communities/…
👥 CryptoJourn
x.com/CryptoJournaalit
y: https://t.co/
3yFdzLLS2O
��
X-profile: https://t.co/fd2b
I2MInh
#CryptoJournaal #AltcoinPedia #CryptoNews #CryptoEducation #CryptoPrices