

We introduce Quantum Spectral Authentication (QSA), a primitive for verifying that a remote quantum endpoint still possesses a previously installed secret quantum resource, such as a hidden state...
From arxiv.org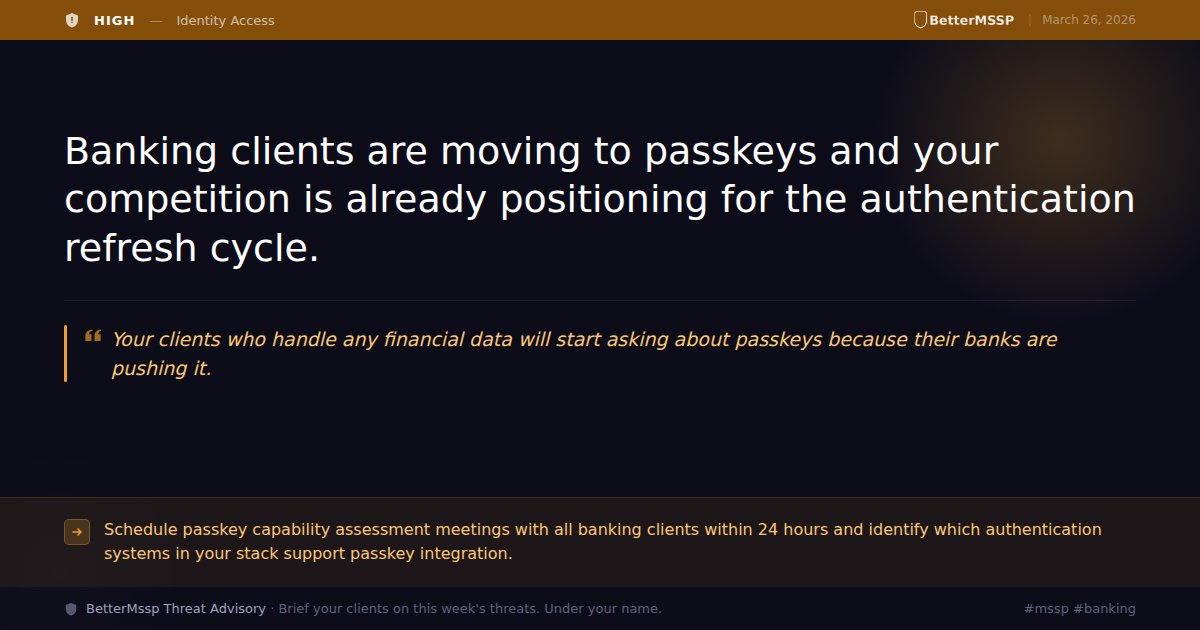
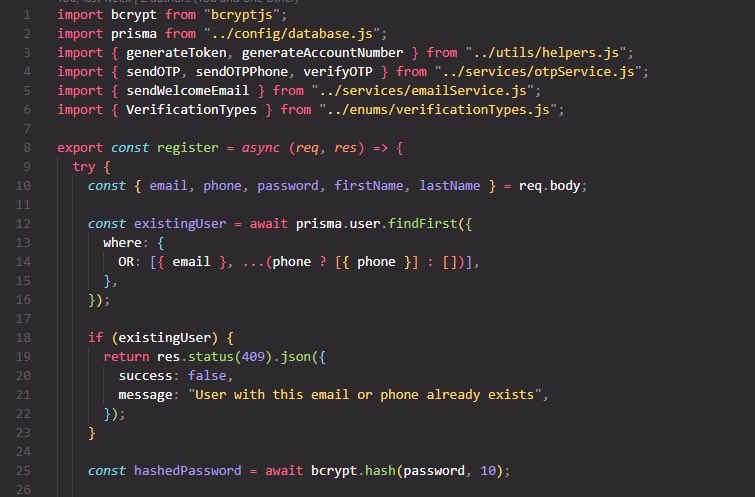
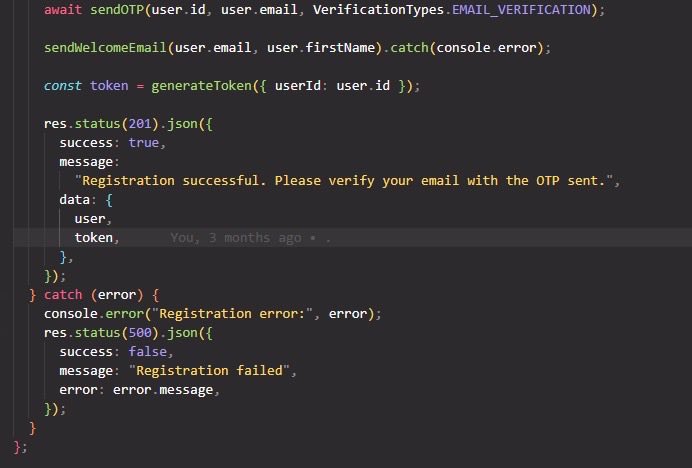
Continuous authentication is a security measure that consistently verifies a user's identity from the moment they log in until their session concludes.
From instasafe.comMWC 2026 showed a clear shift toward network-based authentication. Explore key trends, partnerships, and what this means for the future of identity.
From ipification.com
Yubico, IBM and Auth0 unveil an AI security model that forces human approval for high‑risk automated actions using hardware authentication.
From itbrief.com.au
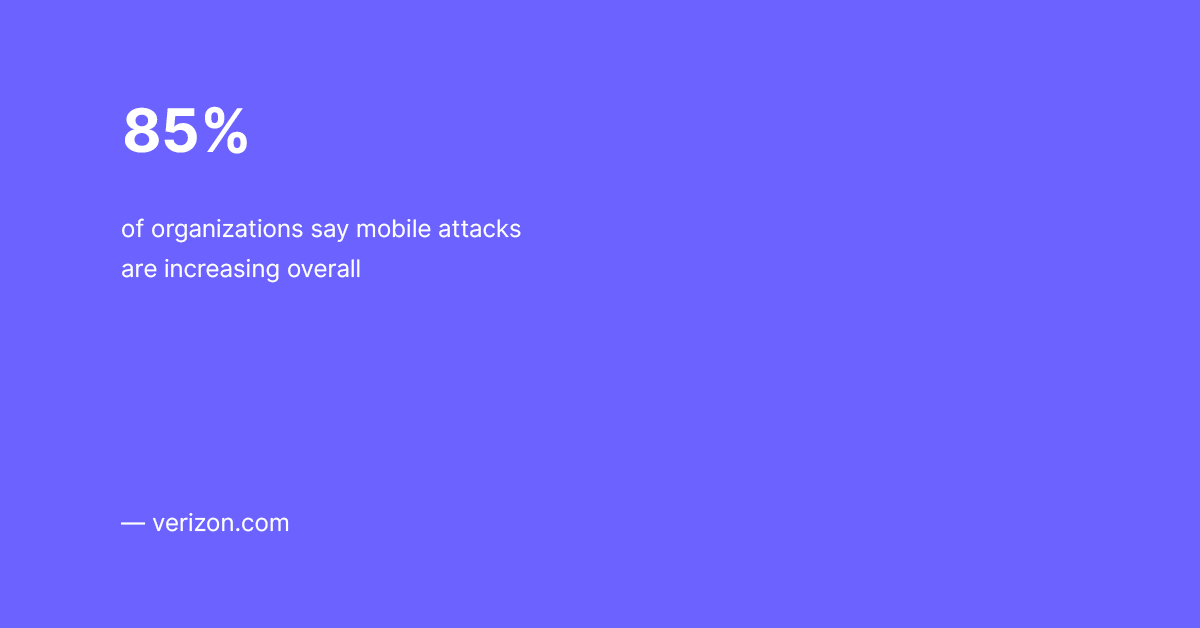
The biggest lesson from 2025's cybersecurity landscape wasn't a new exploit or a novel piece of malware — it was a sobering pattern. Attackers stole passwords, bypassed phishable MFA, and manipulated...
From vmblog.com