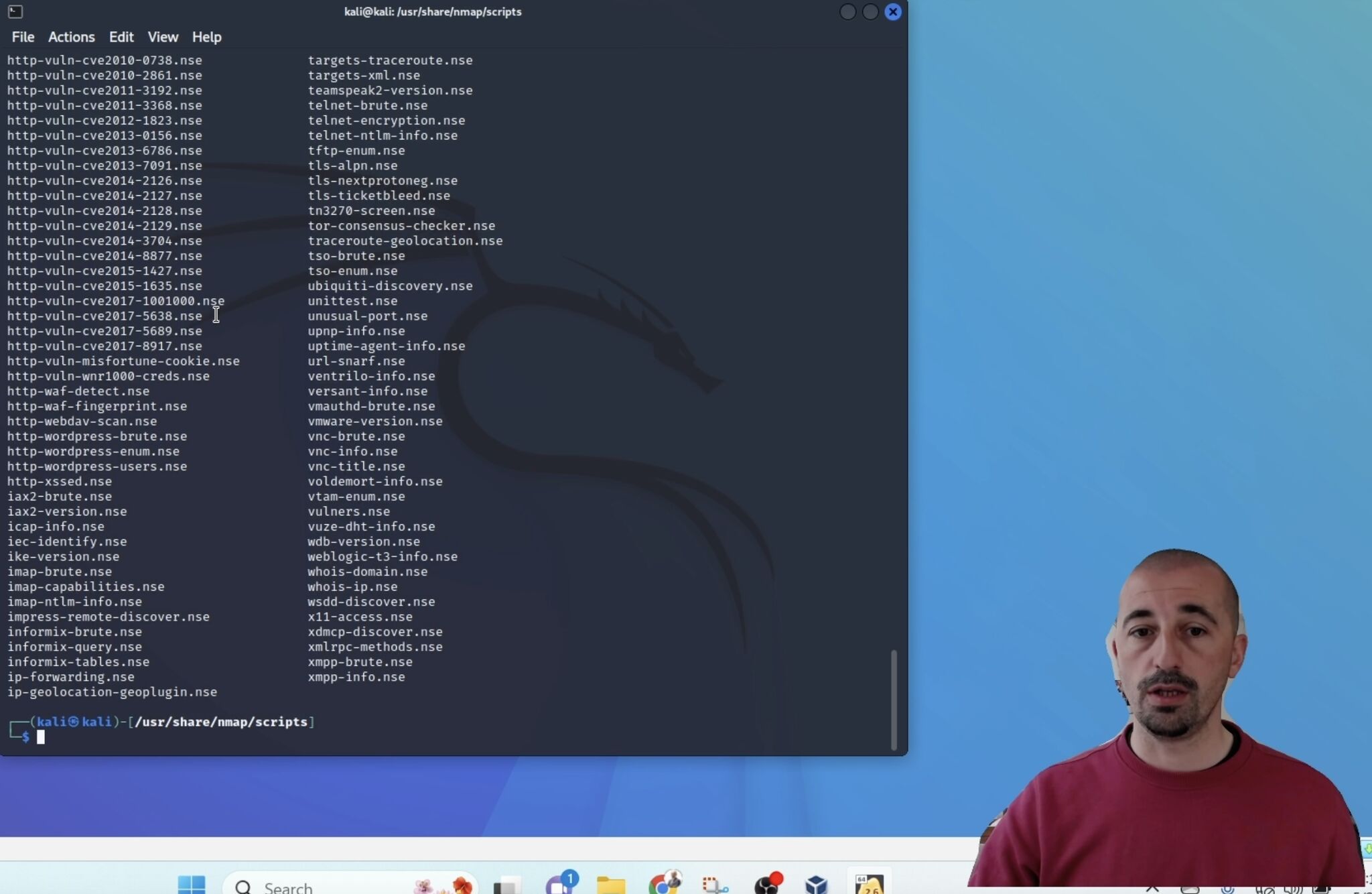
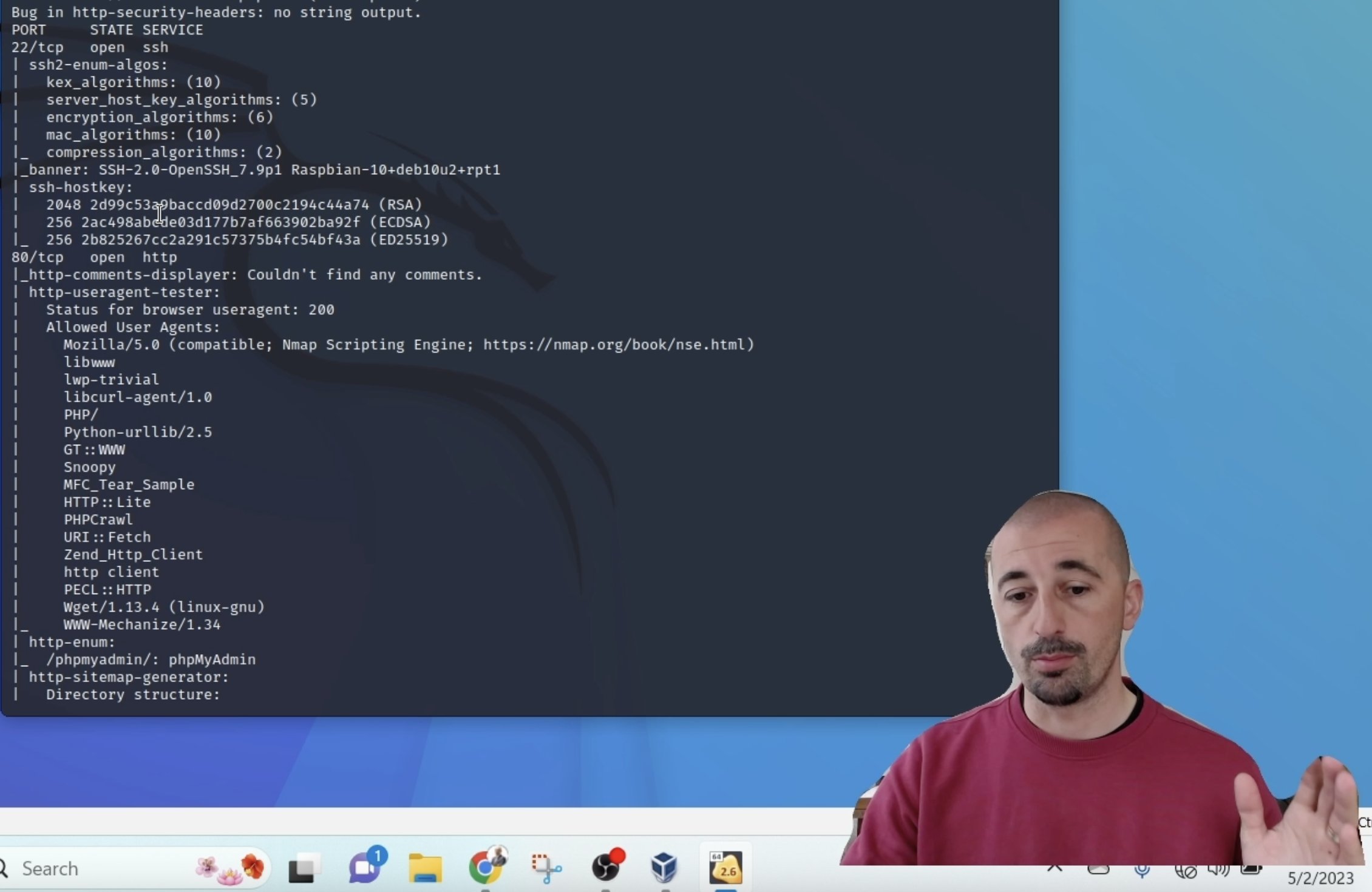
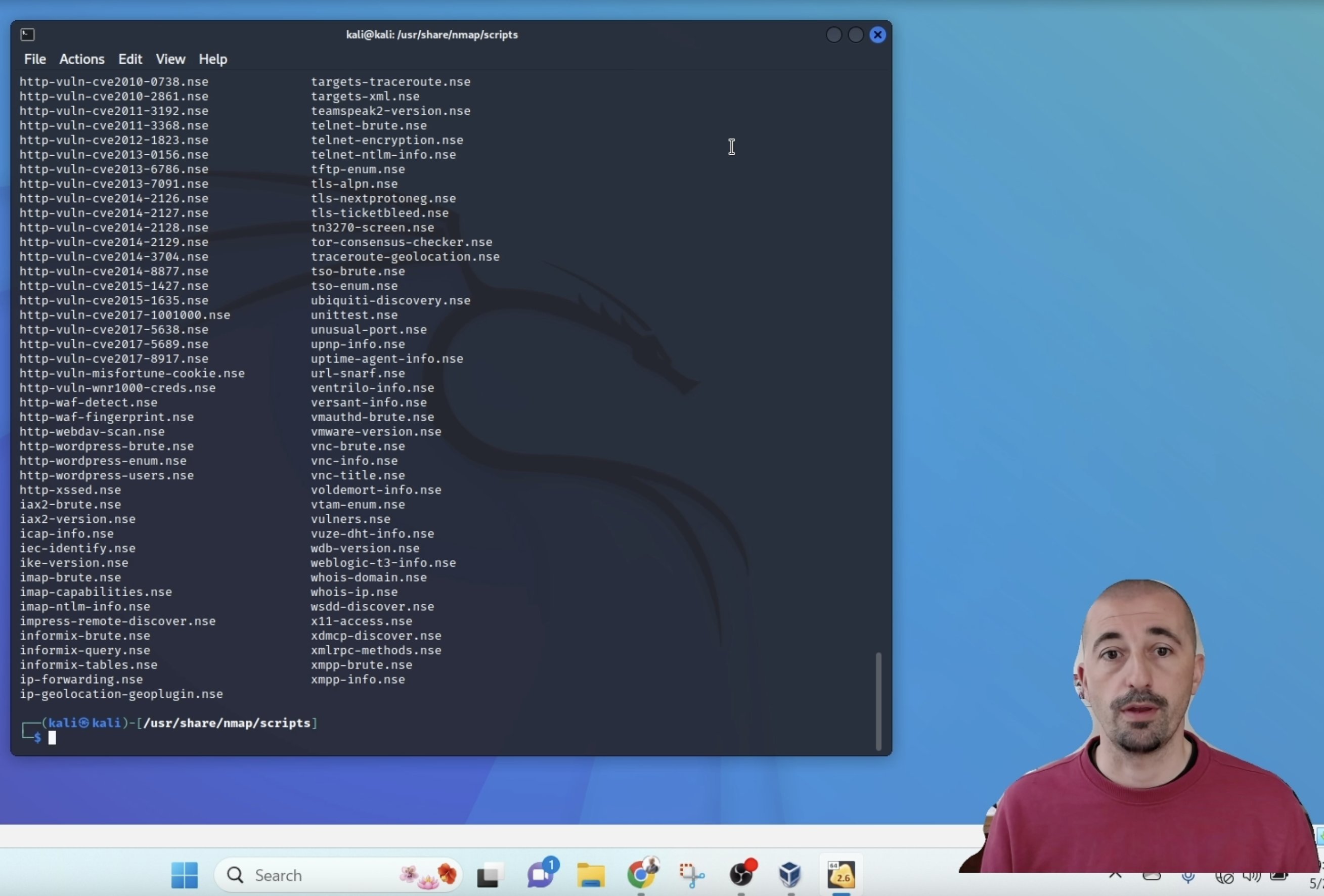
👨🏻💻The demo covers the #vulnerability #management within the #engine of #nmap
Vulnerability, protocols identification on the target machine is conducted in physical #iiot and ICS systems 🦾🚀 by identifying the #attack #vectors and potential #vulnerabacademyict.netcNagb2B
1
60