Story Time:
"Client Dropped Bank Login Creds Like It Was Nothing... Then Ghosted the Authorization Question"
Yesterday a guy DMs me with a "quick" project.
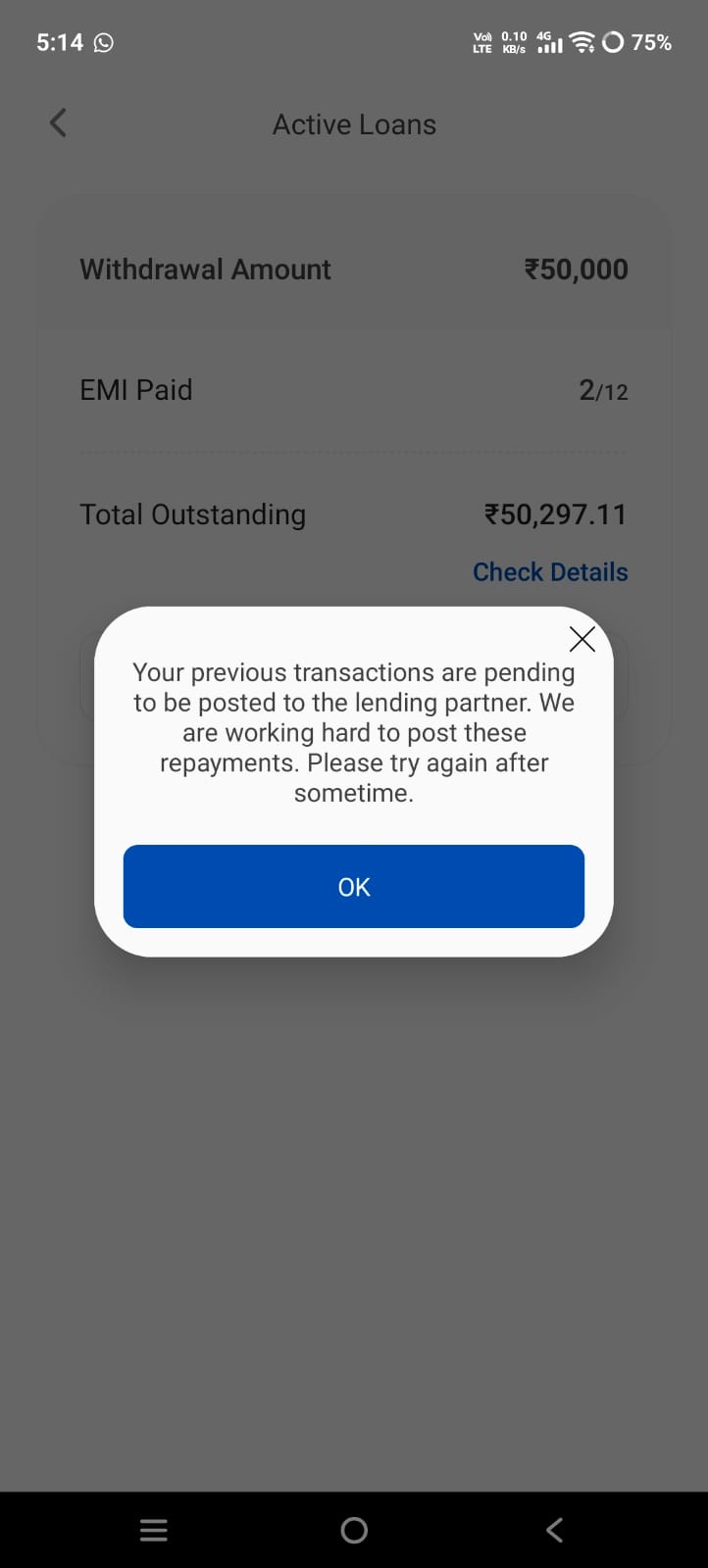
He wants C# code to:
Log into the official RHB Reflex banking app (DuitNow QR)
Generate dynamic QR codes for customer nt status
Cool. Except he sends me the actual login credentials right away:
User Id: AMPOWER
Password: 123456
Then he casually says the app has heavy anti-frida/anti-reverse-engineering protections and he already tried cracking it himself.
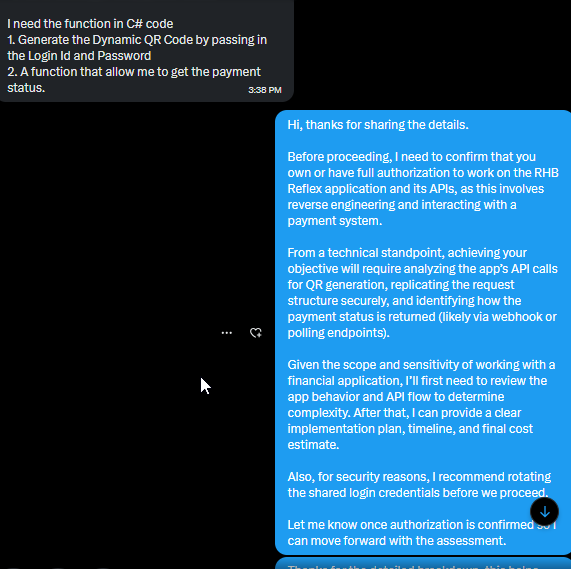
I reply professionally: "Before we touch anything, I need confirmation that you own this app or have full legal authorization from the bank/merchant.
This is a live financial system.
"He replies:
"Yes I have the login details I already sent them"...and completely ignores the authorization part.
No "yes I own the merchant account", no company docs, no NDA, no nothing.
Just "I have the creds bro, let's go".
I double down and explain two paths:
Official PayNet/DuitNow merchant API (the right way)
Or risky reverse-engineering route (which I won't touch without proof)
He never confirms authorization.
Radio silence on that specific question.
This is exactly why security professionals have to be paranoid as hell.
When someone wants you to touch a banking app, payment gateway, or any financial system and they:
Throw real credentials at you like candy push for reverse engineering instead of official integration
Dodge the "do you actually own this?" question
...you STOP Immediately.
This isn't "helping a client". This is the exact moment where you can accidentally become an accessory to something very illegal.
We are not movie hackers. We are the ones who get the call from lawyers (or worse) later.
So the rule I live by now:
"No clear written authorization + financial system = hard pass."Even if the money looks juicy.
Even if they say "bro trust me". Rotate those creds right now if you’re reading this, king Stay safe out there.
#CyberSecurity #RedFlags #EthicalHacking #NeverSkipThePaperwork