#threatreport #MediumCompleteness
RegPhantom Backdoor Threat Analysis | 20-03-2026
Source:
nextron-systems.com/2026/03/20/reg…
Key details below ↓
💀Threats:
Regphantom, Procmon_tool,
🏭Industry: Software_development
🌐Geo: Russia, Singapore, Japan, Chinese, Usa, China
📚TThnics: 0
🤖LLM extracted TTPs:`
T1014, T1027.007, T1027.016, T1112, T1140, T1553.002, T1564, T1620
🧨IOCs:
- Hash: 32
- File: 3
💽Software: Windows kernel, Windows registry
🔢Algorithms: xor, sha256, exhibit
🗂️Win API: CmRegisterCallback, PsLoadedModuleList, PsSetCreateThreadNotifyRoutine, CmUnRegisterCallback, RtlFindExportedRoutineByName
YAR
A: Found
#threatreport:
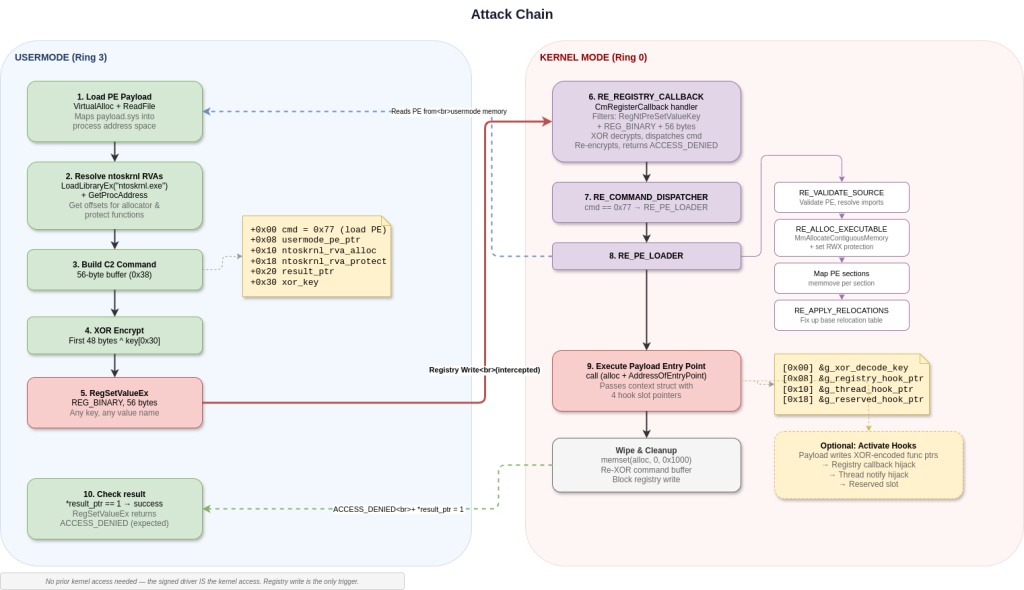
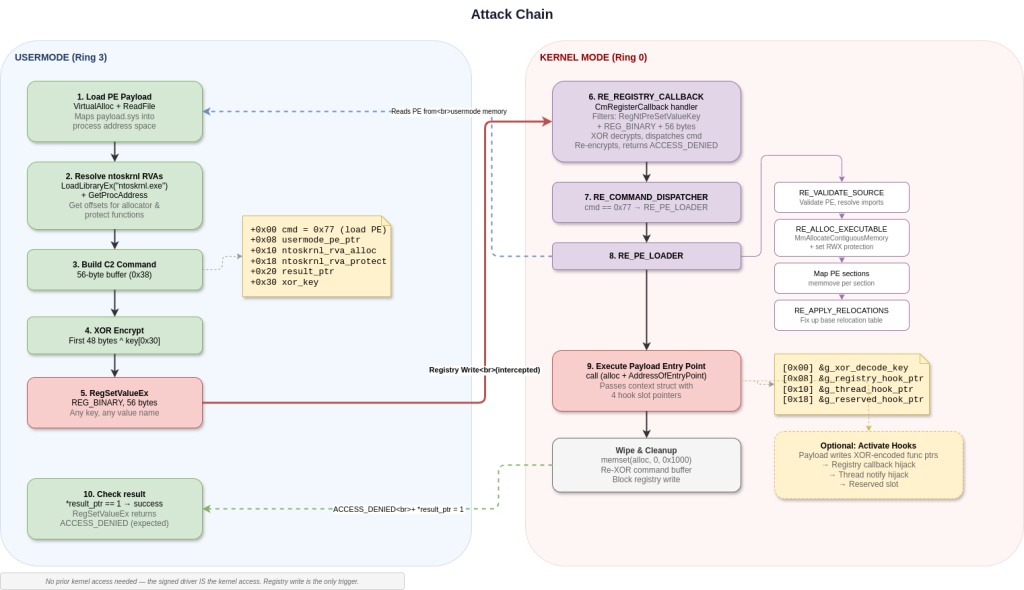
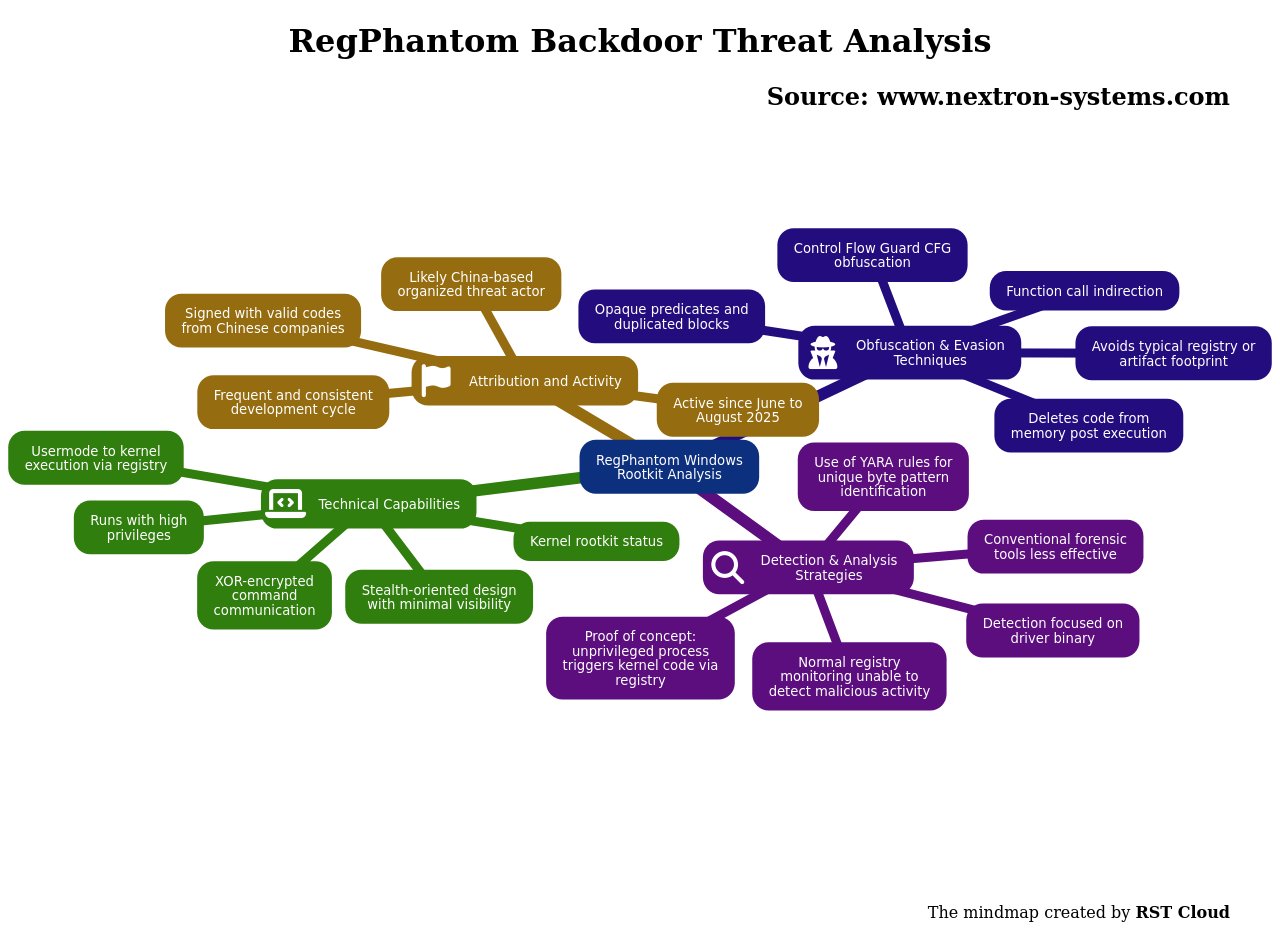
RegPhantom is identified as a sophisticated Windows kernel rootkit that establishes covert usermode-to-kernel execution pipelines by exploiting the Windows registry. This malware allows attackers to execute arbitrary kernel-mode code by sending XOR-encrypted commands through a registry write, which the malicious driver intercepts and processes. Its design prioritizes stealth and minimal visibility, enabling it to execute code at higher privilege levels while masking its activity within normal system operations.
Technical analysis indicates that RegPhantom has been active with several samples identified between June and August 2025, hinting at ongoing development and maintenance by a threat actor likely based in China. The analysis reveals that multiple samples are signed with valid codes from reputable Chinese companies, reinforcing the likelihood of a China-nexus affiliation. Their code-sharing characteristics and a consistent development schedule suggest a well-organized and persistent threat.
RegPhantom uniquely uses Control Flow Guard (CFG) obfuscation, complicating both static and dynamic analysis methods. The control flow graph of the malware is bloated with opaque predicates and duplicated blocks, impeding the resolution of code paths during reverse engineering. Function calls are further obfuscated through a calculated indirection technique, which hinders disassemblers' ability to trace API and internal calls.
During the technical assessment, the analysis successfully recovered the kernel driver but did not locate the original userland executable or a subsequent kernel module intended for loading. However, researchers created a proof-of-concept trigger that demonstrates how an unprivileged usermode process can exploit the registry interaction to load arbitrary modules into kernel space. The malware exploits the registry communication in such a way that monitoring tools perceive it as invalid access, thus escaping detection.
Detection of RegPhantom necessitates a focus on the driver binary itself rather than typical forensic artifacts, as it deliberately avoids leaving any trace in conventional artifact locations such as the registry. The lack of persistent artifacts and the deletion of loaded code from memory post-execution further complicate detection efforts. Consequently, identifying the driver’s unique byte patterns through rules such as YARA analysis is crucial for uncovering RegPhantom’s presence.